Researchers took advantage of a weakness in the encryption scheme of Key Group ransomware and developed a decryption tool that lets some victims to recover their files for free.
The decryptor was created by security experts at threat intelligence company EclecticIQ and works for versions of the malware built in early August.
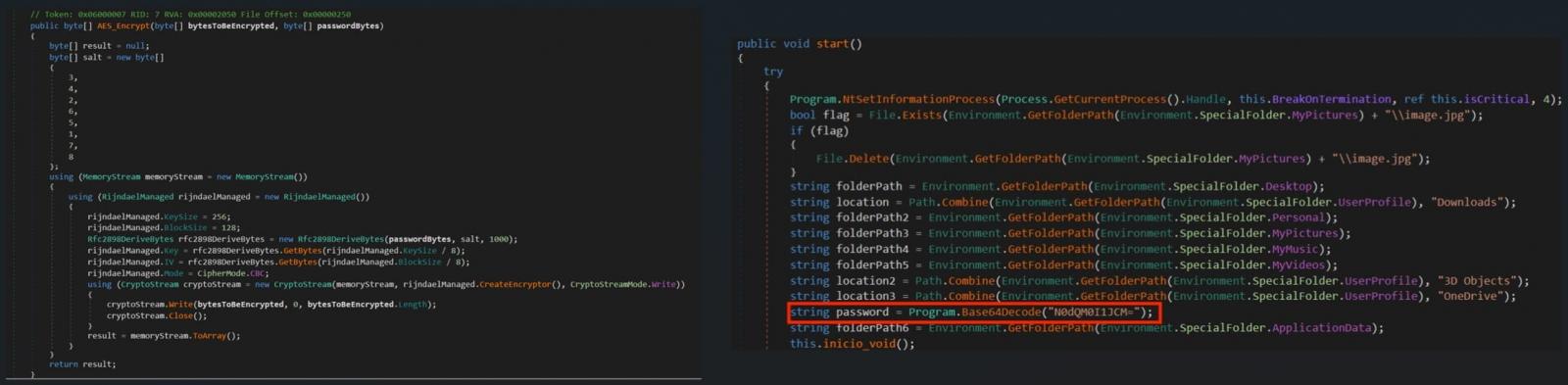
The attackers claimed their malware used “military-grade AES encryption” but the locker uses a static salt across all encryption processes, making the scheme somewhat predictable and the encryption possible to reverse.
“[Key Group ransomware] encrypts victim data using the AES algorithm in Cipher Block Chaining (CBC) mode with a given static password,” explains EclecticIQ
“The password is derived from a key using the Password-Based Key Derivation Function 2 (PBKDF2) with a fixed salt,” the researchers add.
Key Group profile
Key Group is a Russian-speaking threat actor that sprung into action in early 2023, attacking various organizations, stealing data from compromised systems, and then using private Telegram channels to negotiate ransom payments.
Russian threat intelligence firm BI.ZONE has previously reported that Key Group based its ransomware on the Chaos 4.0 builder, while EclecticIQ has seen the group selling on Russian-speaking darknet markets stolen data and SIM cards, as well as sharing doxing data and remote access to IP cameras.
Key Group wipes original files from the victim system after the encryption process, and appeds the .KEYGROUP777TG file extension to all entries.
The attackers use Windows living-off-the-land binaries, the so called LOLBins, to delete Volume Shadow copies, thus preventing system and data restoration without paying a ransom.
Moreover, the malware alters the host addresses of anti-virus products running on the breached system to prevent them from fetching updates.
.png)
How to use the decryptor
The Key Group ransomware decryptor is a Python script (shared in Appendix A section of the report). Users can save it as a Python file and then run it using the following command:
python decryptor.py /path/to/search/directory
The script will search the target directory and its subdirectories for files with the .KEYGROUP777TG extension and will decrypt and save the unlocked content with the original filename (decoded from the base64 string).
Note that there are some Python libraries required, especially the cryptography package.
It is always prudent to back up your (encrypted) data before using any decryptor, as the process may lead to irreversible data corruption and permanent data loss.
The release of EclecticIQ’s decryptor might prompt Key Group to address the vulnerabilities in their ransomware, making future versions harder to decrypt. Nevertheless, the tool remains valuable for individuals affected by current versions.








Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now