A decryption tool for a modified version of the Conti ransomware could help hundreds of victims recover their files for free.
The utility works with data encrypted with a strain of the ransomware that emerged after the source code for Conti was leaked last year in March [1, 2].
Hundreds of victims encrypted
Researchers at cybersecurity company Kaspersky found the leak on a forum where the threat actors released a cache of 258 private keys from a modified version of the Conti ransomware.
The variant was used in attacks against various private and public organizations over the past year by a ransomware group that some researchers track as MeowCorp.
Ransomware researcher Amigo-A told BleepingComputer that the threat actors published the data on a Russian-speaking forum in February 2022, which contained a link to an archive containing decryption keys, decryptor executables, and the decryptor source code.
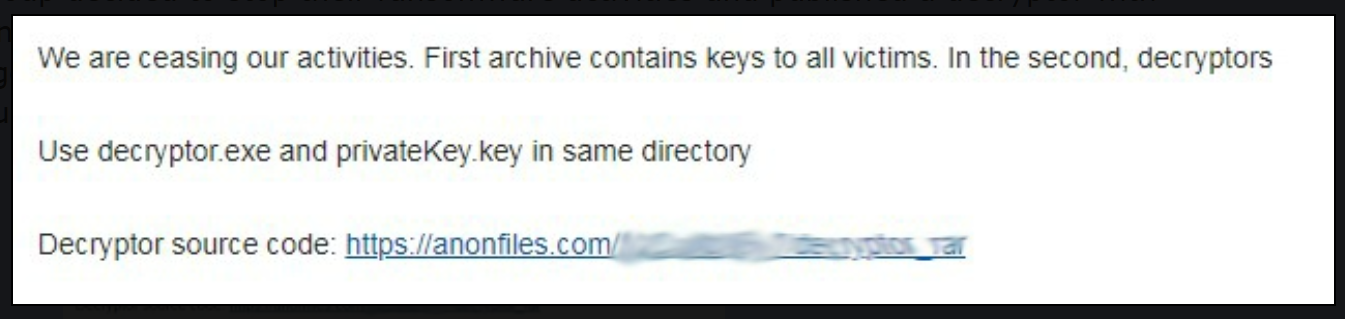
source: Amigo-A
Kaspersky analyzed the keys and found them to be associated with a Conti variant they discovered in December 2022. However, the strain had been circulating since at least August.
“The leaked private keys are located in 257 folders (only one of these folders contains two keys),” Kaspersky says in a press release today.
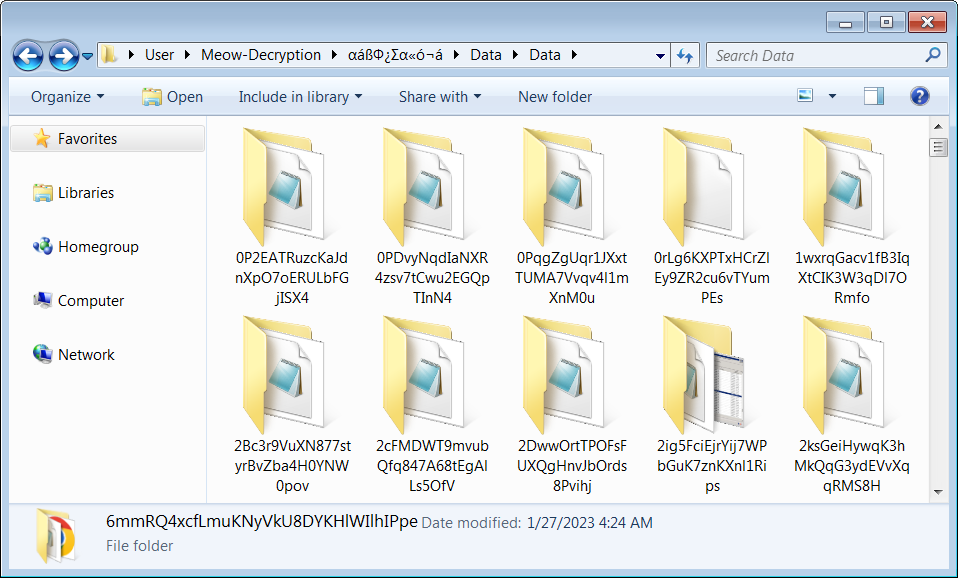
source: BleepingComputer
BleepingComputer learned that the attacks using the Conti-based encryptor targeted mostly Russian organizations.
The researchers add that some of the folders included previously generated decryptors along with other files, i.e. photos and documents, that were likely used to show victims that the decryption works.
34 of the folders contained explicit names for victim organizations in the government sector in countries in Europe and Asia.
Fedor Sinitsyn, lead malware analyst at Kaspersky, told BleepingComputer that the names in the rest of the folders were hashed or encoded.
Based on this and the number of decryptors available in the leak, Kaspersky says that it can be assumed that the modified Conti strain was used to encrypt 257 victims and that 14 of them paid the attackers to recover locked data.
The private keys were created between November 13, 2022 and February 5, 2023, which is a good indication about the timeline of the attacks. Sinitsyn told us that the infection dates for the victims that contacted Kaspersky for decryption fell into that time range.
Kaspersky added the decryption code and the 258 private keys to its RakhniDecryptor, a tool that can recover files encrypted by more than two dozen ransomware strains.
According to Kaspersky, the decrytor can recover files encrypted by the modified Conti variant that used the following name pattern and extensions:
- <file_name>.KREMLIN
- <file_name>.RUSSIA
- <file_name>.PUTIN
Conti ransomware's demise
For about three years, the Conti gang ran one of the most active and lucrative ransomware-as-a-service operations, targeting big organizations and demanding large ransoms to decrypt the data they locked.
Considered the successor of Ryuk ransomware, the Conti operation started in December 2019 and, with the help of TrickBot operators, it became a dominant threat by July 2020.
The gang wreaked havoc unabated for a year and adopted new tactics (e.g. data theft, leak site) to force victims into paying the ransom.
In August 2021, a disgruntled Conti affiliate leaked information about some of the group members along with the gang’s attack method and training manuals.
The Russian invasion of Ukraine in February last year created more internal friction as core members sided with Russia.
This led a researcher who had been snooping on the operation to leak thousands of messages exchanged between Conti operators and affiliates.
The researcher’s revenge continued through March by leaking the source code for the ransomware encryptor, decryptor, and builder, as well as the administrative panels [1, 2].
It didn’t take long for the operation to break down and in May 2022 the Conti team leaders took offline the infrastructure and announced that the brand no longer existed.
Conti leadership partnered with other gangs in the extortion business and the other members migrated to other ransomware operations.
The U.S. government assesses that Conti was one of the most lucrative ransomware operations, making thousands of victims and amassing more than $150 million in ransom payments.
The damage caused to U.S. companies determined the U.S. Department of State to offer a reward of up to $15 million for information that identified and located Conti leaders and affiliates.
Update [March 16, 16:39 EST]: Article updated with information from Kaspersky we received after publishing time.








Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now