
A new Android malware named NGate can steal money from payment cards by relaying to an attacker's device the data read by the near-field communication (NFC) chip.
Specifically, NGate enables attackers to emulate victims' cards and make unauthorized payments or withdrawal cash from ATMs..
The campaign has been active since November 2023 and is linked to a recent report from ESET on the increased use of progressive web apps (PWAs) and advanced WebAPKs to steal banking credentials from users in the Czechia.
In research published today, the cybersecurity company says that NGate malware was also used during the campaign in some cases to perform direct cash theft.
Stealing card data via NFC chip
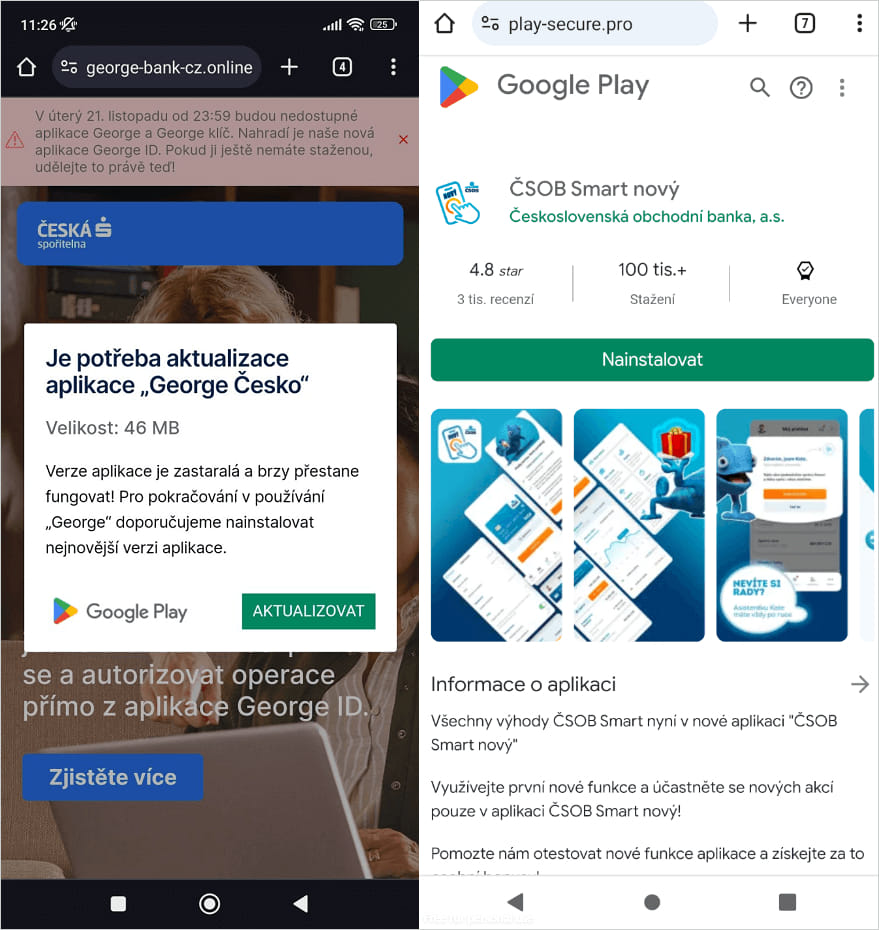
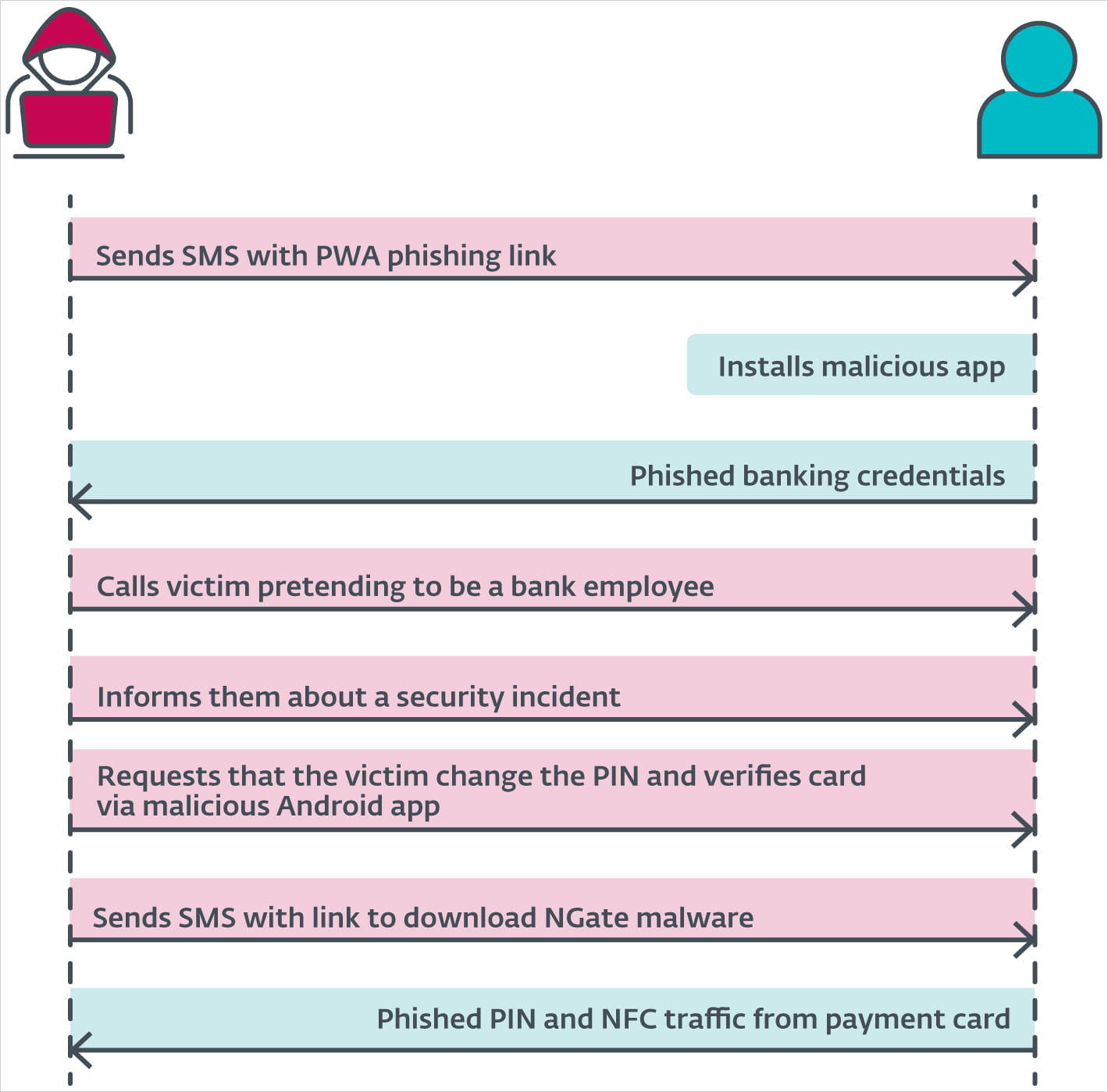
The attacks start with malicious texts, automated calls with pre-recorded messages, or malvertising to trick victims into installing a malicious PWA, and later WebAPKs, on their devices.
These web apps are promoted as urgent security updates and use the official icon and login interface of the targeted bank to steal client access credentials.
Source: ESET
These apps do not require any permission when installed. Instead, they abuse the API of the web browser they run in to get the necessary access to the device's hardware components.
Once the phishing step is done via the WebAPK, the victim is tricked into also installing NGate via a subsequent step in the second attack phase.
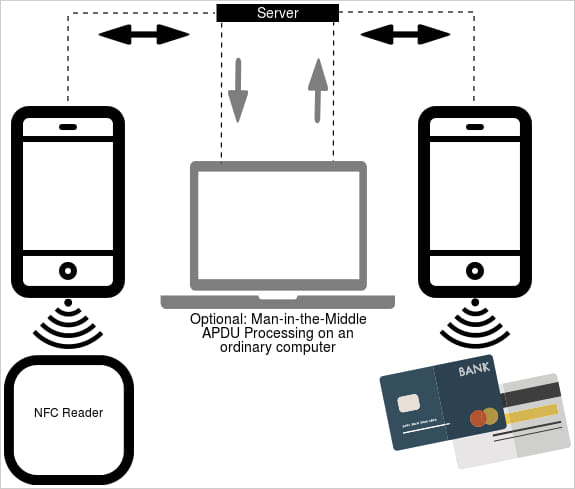
Upon installation, the malware activates an open-source component called 'NFCGate' that was developed by university researchers for NFC testing and experimentation.
The tool supports on-device capturing, relaying, replaying, and cloning features, and does not always require the device to be "rooted" in order to work.
NGate uses the tool to capture NFC data from payment cards in close proximity to the infected device and then relay it to the attacker's device, either directly or through a server.
The attacker may save this data as a virtual card on their device and replay the signal on ATMs that use NFC to withdraw cash, or make a payment at a point-of-sale (PoS) system.
Source: ESET
In a video demonstration, ESET's malware researcher Lukas Stefanko also shows how the NFCGate component in NGate can be used to scan and capture card data in wallets and backpacks. In this scenario, an attacker at a store could receive the data through a server and make a contactless payment using the victim's card.
Stefanko notes that the malware can also be used to clone the unique identifiers of some NFC access cards and tokens to get into restricted areas.
Acquiring the card PIN
A cash withdrawal at most ATMs requires the card's PIN code, which the researchers say that it is obtained by social engineering the victim.
After the PWA/WebAPK phishing step is done, the scammers call the victim, pretending they are a bank employee, informing them of a security incident that impacts them.
They then send an SMS with a link to download NGate, supposedly an app to be used for verifying their existing payment card and PIN.
Once the victim scans the card with their device and enters the PIN to "verify" it on the malware's phishing interface, the sensitive information is relayed to the attacker, enabling the withdrawals.
Source: ESET
The Czech police already caught one of the cybercriminals performing these withdrawals in Prague, but as the tactic may gain traction, it poses a significant risk for Android users.
ESET also highlights the possibility of cloning area access tags, transport tickets, ID badges, membership cards, and other NFC-powered technologies, so direct money loss isn't the only bad scenario.
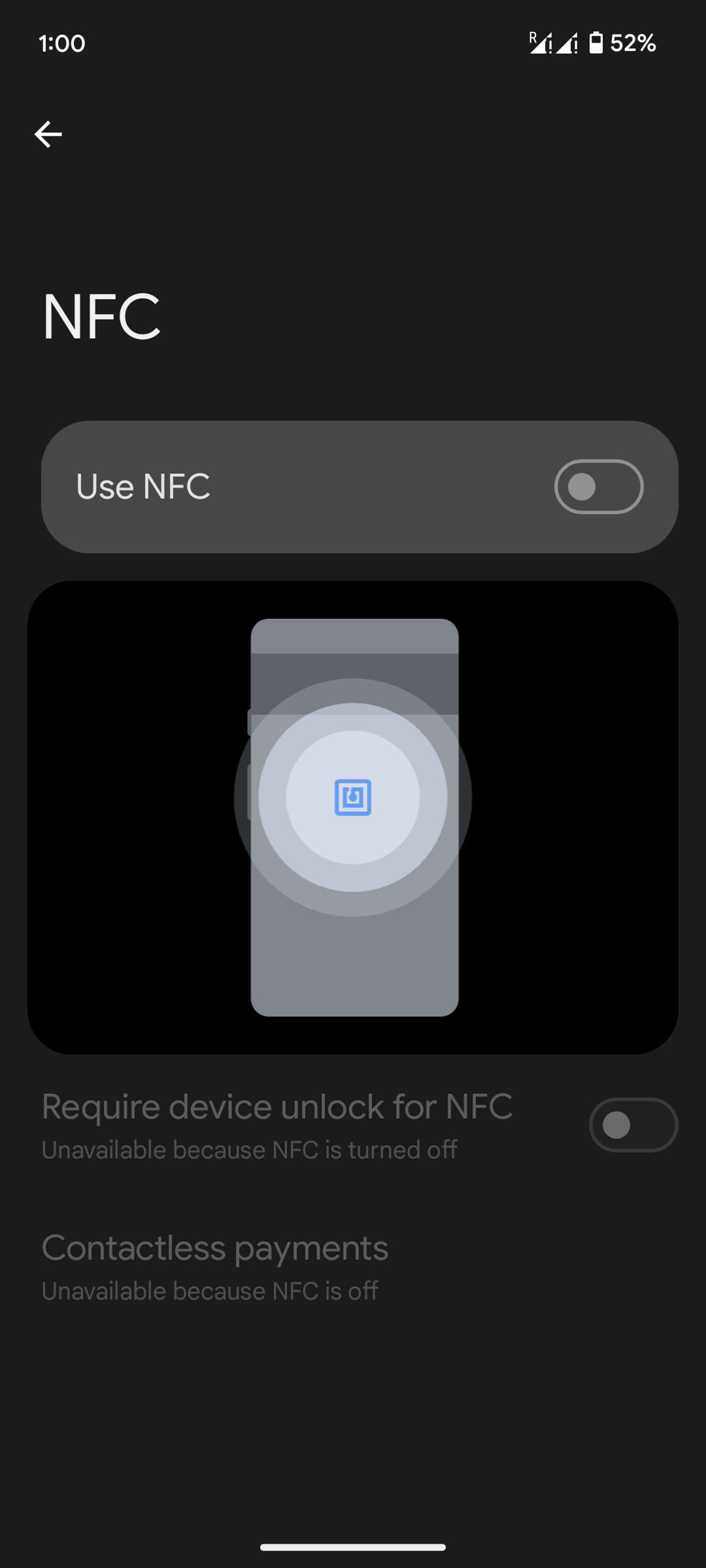
If you are not actively using NFC, you can mitigate the risk by disabling your device's NFC chip. On Android, head to Settings > Connected devices > Connection preferences > NFC and turn the toggle to the off position.
If you need NFC activated at all times, scrutinize all app permissions and restrict access only to those that need it; only install bank apps from the institution's official webpage or Google Play, and ensure the app you're using isn't a WebAPK.
WebAPKs are usually very small in size, are installed straight from a browser page, do not appear under '/data/app' like standard Android apps, and show atypically limited information under Settings > Apps.
Update 8/23 - A Google spokesperson told BleepingComputer that Google Play Protect, Android's default malware scanner, detects NGate:
"Based on our current detections, no apps containing this malware are found on Google Play.
Android users are automatically protected against known versions of this malware by Google Play Protect, which is on by default on Android devices with Google Play Services.
Google Play Protect can warn users or block apps known to exhibit malicious behavior, even when those apps come from sources outside of Play." - Google spokesperson









Comments
XSp - 2 months ago
Huh... who would have thought that the simplest and most obvious security worry about NFC payment systems would have turned out justified like this.
Lexter99 - 2 months ago
Hmmmm, I'm calling BS. That's not how NFC card payments work. Doesn't matter what permissions you have you can't just capture a card through NFC and replay it later. Nothing about this story adds up at at all. It's equivalent to saying you're going to capture the beginning of an SSL session and replay that to break an HTTPS session. That's just not how PKI works. I've no idea where this is coming from, but it doesn't pass the credibility test
powerspork - 2 months ago
I would think of this more like those car key fob relays used to steal modern cars. They get the signal from the fob and relay it to another device much farther away that pretends to be the key. This way, the key inside is relayed and spoofed to the other device next to or inside the car, and the car doesn't know different. The thief gets in and drives off.
Combine this with the PIN reset, and the card (especially if in a pop socket on the back of a phone) can be "relayed" to an attacker with a device at an ATM nowhere near the card holder. You don't need to break the cryptography. It works as designed but is no longer limited to a few cm away.
Lexter99 - 2 months ago
Nope, you cannot MITM a PKI communication. Same principle as an HTTPS/SSL session - doesn't matter if you intercept the traffic between sender and receiver during set up, you still cannot decrypt the traffic. That's fundamental to secure comms on the internet. Same here. And if you could, there would have long been a wave of attacks with people "skimming" contactless payments. Again. You can see the RF signals but you cannot get inside the encryption
powerspork - 2 months ago
I literally said in my post that you don't need to break the cryptography. That's not what they're doing. They are making the card, which is not in their hand, usable as if it was by connecting to it through the phone and sending the traffic (without decrypting it) to a remote point. The PIN reset is part of the attack so they have everything they need to make a withdrawal.