
Hackers are targeting Windows machines using the ZIP file concatenation technique to deliver malicious payloads in compressed archives without security solutions detecting them.
The technique exploits the different methods ZIP parsers and archive managers handle concatenated ZIP files.
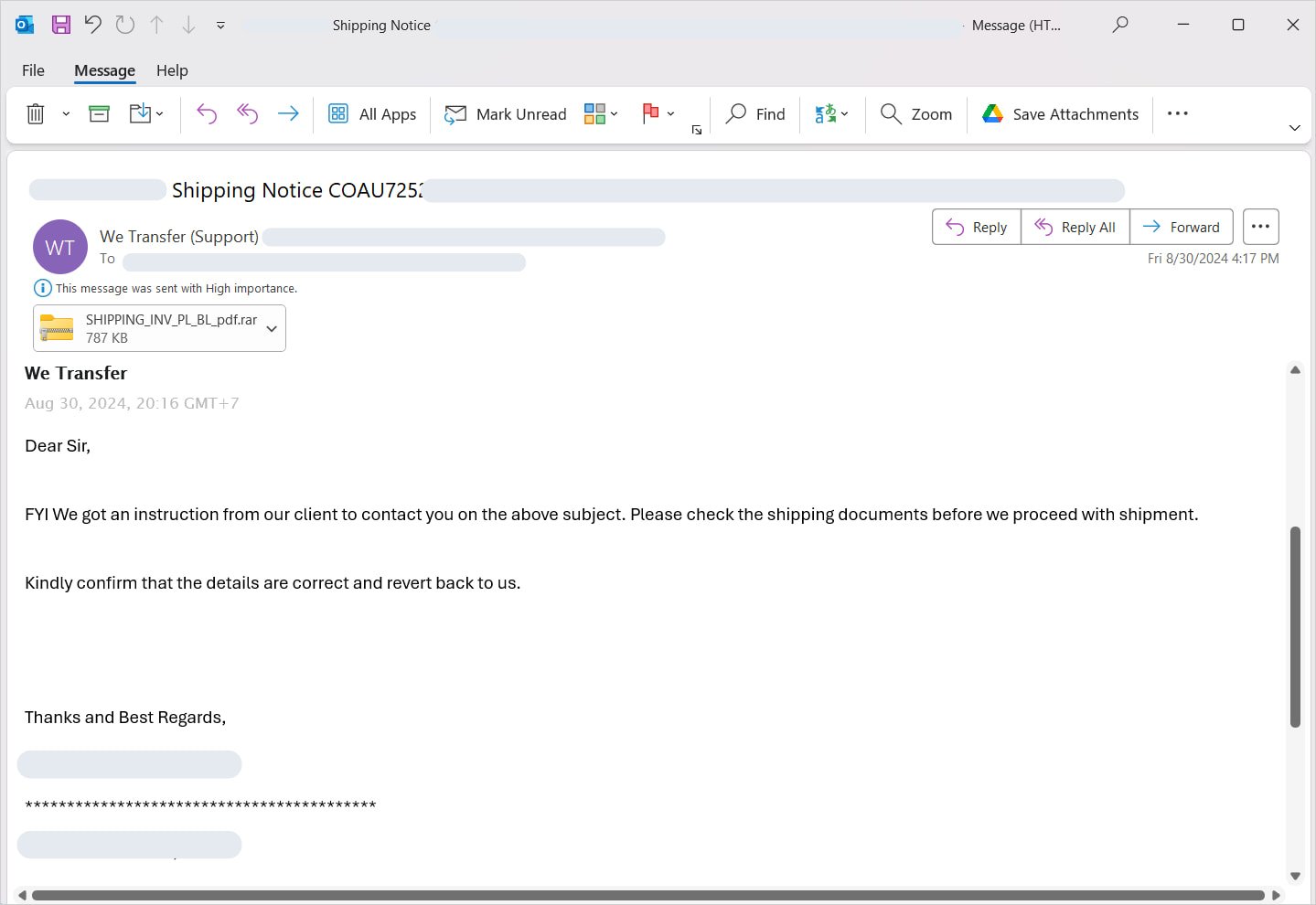
This new trend was spotted by Perception Point, who discovered a a concatentated ZIP archive hiding a trojan while analyzing a phishing attack that lured users with a fake shipping notice.
The researchers found that the attachment was disguised as a RAR archive and the malware leveraged the AutoIt scripting language to automate malicious tasks.
Source: Perception Point
Hiding malware in “broken” ZIPs
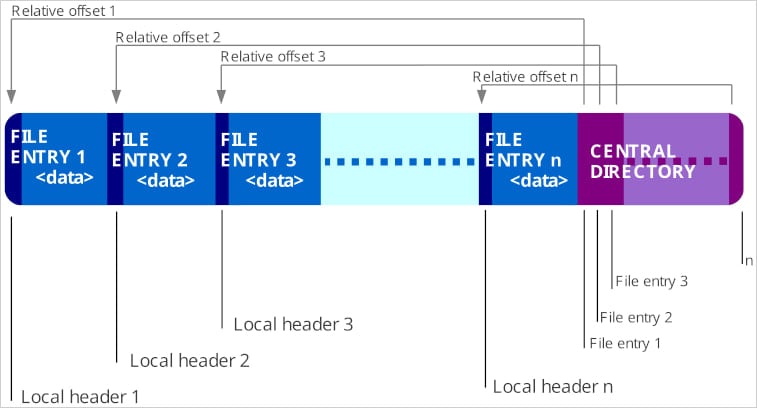
The first stage of the attack is the preparation, where the threat actors create two or more separate ZIP archives and hide the malicious payload in one of them, leaving the rest with innocuous content.
Next, the separate files are concatenated into one by appending the binary data of one file to the other, merging their contents into one combined ZIP archive.
Although the final result appears as one file, it contains multiple ZIP structures, each with its own central directory and end markers.
Source: Perception Point
Exploiting ZIP app flaws
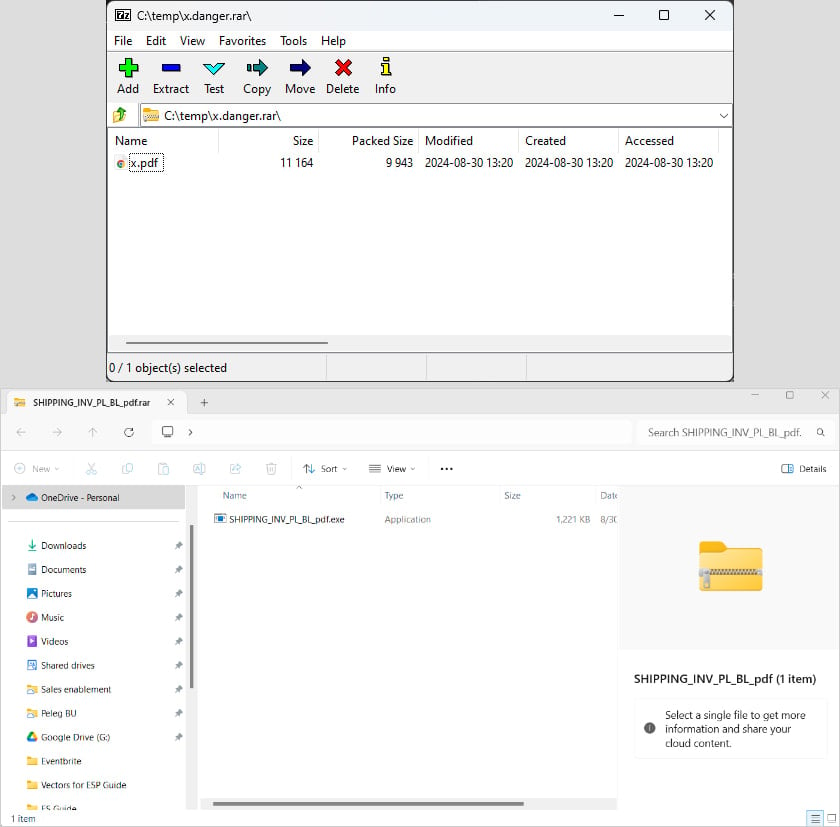
The next phase of the attack relies on how ZIP parsers handle concatenated archives. Perception Point tested 7zip, WinRAR, and Windows File Explorer to different results:
- 7zip only reads the first ZIP archive (which could be benign) and may generate a warning about additional data, which users may miss
- WinRAR reads and displays both ZIP structures, revealing all files, including the hidden malicious payload.
- Windows File Explorer may fail to open the concatenated file or, if renamed with a .RAR extension, might display only the second ZIP archive.
Depending on the app’s behavior, the threat actors may fine-tune their attack, such as hiding the malware in the first or the second ZIP archive of the concatenation.
Trying the malicious archive from the attack on 7Zip, Perception Point researchers saw that only a harmless PDF file was shown. Opening it with Windows Explorer, though, revealed the malicious executable.
Source: Perception Point
To defend against concatenated ZIP files, Perception Point suggests that users and organizations use security solutions that support recursive unpacking.
Generally, emails attaching ZIPs or other archive file types should be treated with suspicion, and filters should be implemented in critical environments to block the related file extensions.








Comments
Cesafro54 - 2 days ago
Nice Analysis!
Speeddymon - 2 days ago
This reminds me of how we accomplished getting root access to Android 2.1 way back in 2010 using a concatenated zip file and exploiting a bug in the Android update tool to insert a modified update package.