
SolarWinds has released a hotfix for a critical Web Help Desk vulnerability that allows attackers to log into unpatched systems using hardcoded credentials.
Web Help Desk (WHD) is an IT help desk software widely used by government agencies, large corporations, and healthcare and education organizations to automate and streamline help desk management tasks. SolarWinds' IT management products are used by over 300,000 customers worldwide.
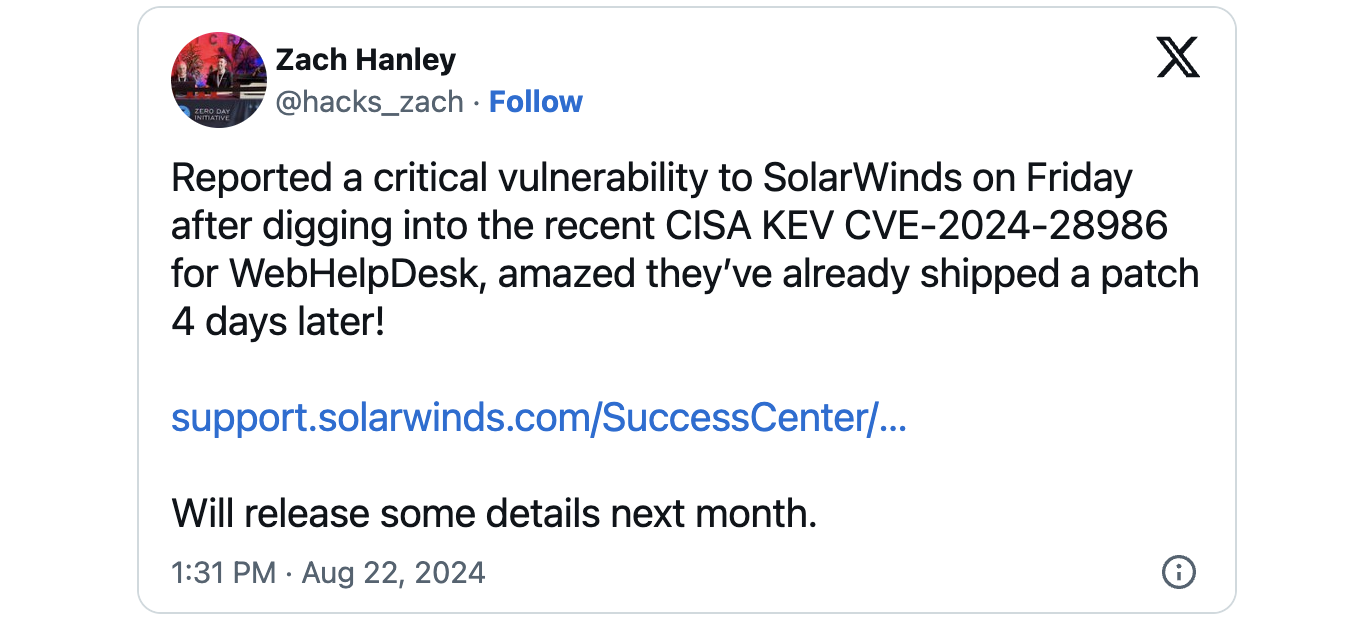
The security flaw (CVE-2024-28987) addressed this Wednesday enables unauthenticated attackers to access internal functionality and modify data on targeted devices following successful exploitation. This vulnerability was discovered and reported by Zach Hanley, vulnerability researcher at Horizon3.ai.
SolarWinds has yet to publish a security advisory for this WHD vulnerability on its Trust Center and has not disclosed whether CVE-2024-28987 was exploited in the wild before Web Help Desk 12.8.3 Hotfix 2 was released.
The company provides detailed instructions on installing and removing the hotfix, warning admins to upgrade vulnerable servers to Web Help Desk 12.8.3.1813 or 12.8.3 HF1 before deploying this week's hotfix.
It also recommends creating backups of all original files before replacing them during the hotfix installation process to avoid potential issues if the hotfix fails or isn't applied correctly.
Hotfix also fixes actively exploited Web Help Desk RCE bug
The same hotfix also includes the fix for a critical WHD remote code execution vulnerability (CVE-2024-28986), which was addressed with another hotfix on August 14 and was tagged by CISA as exploited in attacks two days later.
CISA added CVE-2024-28986 to its KEV catalog one week ago, mandating federal agencies to patch all WHD servers on their network by September 5, as required by the Binding Operational Directive (BOD) 22-01.
"These types of vulnerabilities are frequent attack vectors for malicious cyber actors and pose significant risks to the federal enterprise," the cybersecurity agency warned.
Earlier this year, SolarWinds patched over a dozen critical remote code execution (RCE) flaws in its Access Rights Manager (ARM) software—five in February and eight in July.
In June, cybersecurity firm GreyNoise also warned that threat actors were exploiting a SolarWinds Serv-U path-traversal vulnerability shortly after SolarWinds released a hotfix.









Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now