
A recently disclosed Microsoft SharePoint remote code execution (RCE) vulnerability tracked as CVE-2024-38094 is being exploited to gain initial access to corporate networks.
CVE-2024-38094 is a high-severity (CVSS v3.1 score: 7.2) RCE flaw impacting Microsoft SharePoint, a widely used web-based platform functioning as an intranet, document management, and collaboration tool that can seamlessly integrate with Microsoft 365 apps.
Microsoft fixed the vulnerability on July 9, 2024, as part of the July Patch Tuesday package, marking the issue as "important."
Last week, CISA added CVE-2024-38094 to the Known Exploited Vulnerability Catalog but did not share how the flaw was exploited in attacks.
A new report from Rapid7 this week sheds light on how attackers exploit the SharePoint flaw, stating it was used in a network breach they were brought to investigate.
"Our investigation uncovered an attacker who accessed a server without authorization and moved laterally across the network, compromising the entire domain," reads the related report.
"The attacker remained undetected for two weeks. Rapid7 determined the initial access vector to be the exploitation of a vulnerability, CVE 2024-38094, within the on-premise SharePoint server."
Using AVs to impair security
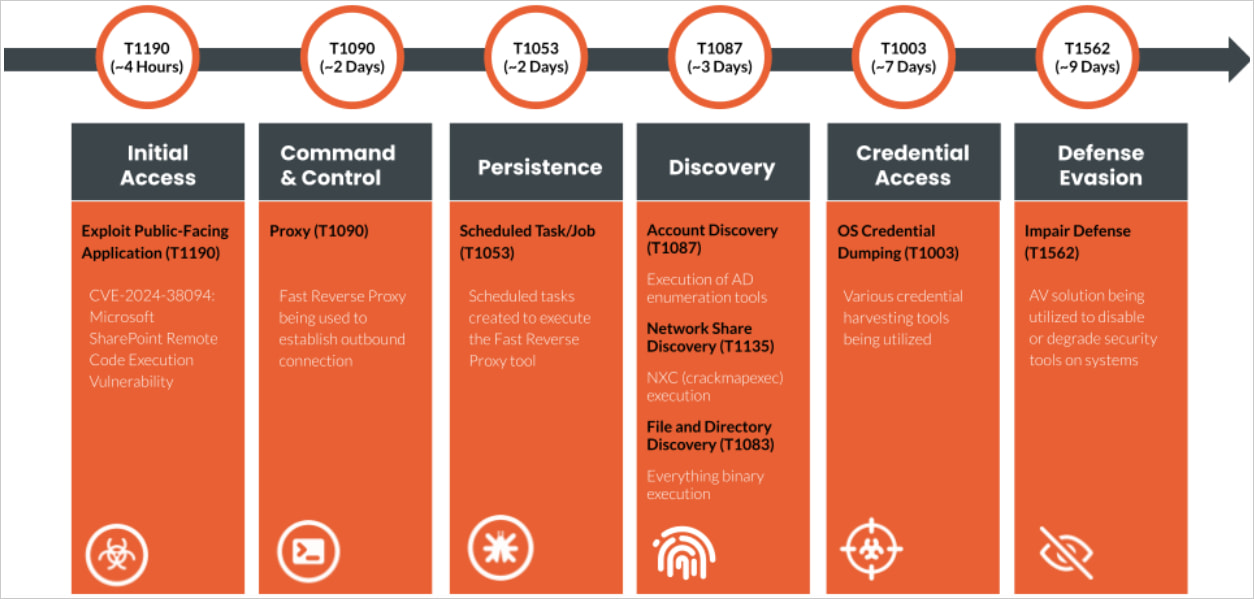
Rapid7 now reports that attackers used CVE-2024-38094 to gain unauthorized access to a vulnerable SharePoint server and plant a webshell. The investigation showed that the server was exploited using a publicly disclosed SharePoint proof-of-concept exploit.
Leveraging their initial access, the attacker compromised a Microsoft Exchange service account with domain administrator privileges, gaining elevated access.
Next, the attacker installed the Horoung Antivirus, which created a conflict that disabled security defenses and impaired detection, allowing them to install Impacket for lateral movement.
Specifically, the attacker used a batch script ('hrword install.bat') to install Huorong Antivirus on the system, set up a custom service ('sysdiag'), execute a driver ('sysdiag_win10.sys'), and run 'HRSword.exe' using a VBS script.
This setup caused multiple conflicts in resource allocation, loaded drivers, and active services, causing the company's legitimate antivirus services to crash being rendered powerless.
Source: Rapid7
In the following stage, the attacker used Mimikatz for credential harvesting, FRP for remote access, and set up scheduled tasks for persistence.
To avoid detection, they disabled Windows Defender, altered event logs, and manipulated system logging on the compromised systems.
Additional tools such as everything.exe, Certify.exe, and kerbrute were used for network scanning, ADFS certificate generation, and brute-forcing Active Directory tickets.
Third-party backups were also targeted for destruction, but the attackers failed in their attempts to compromise those.
Although attempting to erase backups is typical in ransomware attacks, to prevent easy recovery, Rapid7 did not observe data encryption, so the type of the attack is unknown.
With active exploitation underway, system administrators who have not applied SharePoint updates since June 2024 must do so as soon as possible.









Comments
horsedoggs - 1 week ago
With AD Connect It baffles me to why any company needs to run on prem SharePoint/exchange in 2024.
Zurv - 1 week ago
Cost? It is pretty much free to run it on prem.
SharePoint or Exchange server is likely in SA licensing. So, like $125 a year. Access to both is part of a Core Cal. That is also cheap.
We run hybrid exchange. (also about 2,000 users. Only 150 are on Exchange-online) - We could buy a new Exchange server every 2 +month for the cost of Exchange-online. (We've had zero outages or problems with on our prem server. If we did? We could rebuild the server and recover in a few hours.)
That said, to leave a server to directly talk to the internet these days is crazy. We don't use sharepoint, but if we did we'd put it behind a VPN or portal. Not raw dog on the internet.
deltasierra - 1 week ago
Crashing security software should be a noisy affair; the fact that this wasn't a major detection event shows the lack of decent security posture; same with disabling Windows Defender.
Plenty of activity here that any SIEM would pick up. Smaller org as I'd like to think that's not optional these days...
I have to agree with horsedoggs. It might be cheap but why take on the risk?