
A recent variant of the GarrantyDecrypt ransomware has been found that pretends to be from the security team for Proton Technologies, the company behind ProtonMail and ProtonVPN.
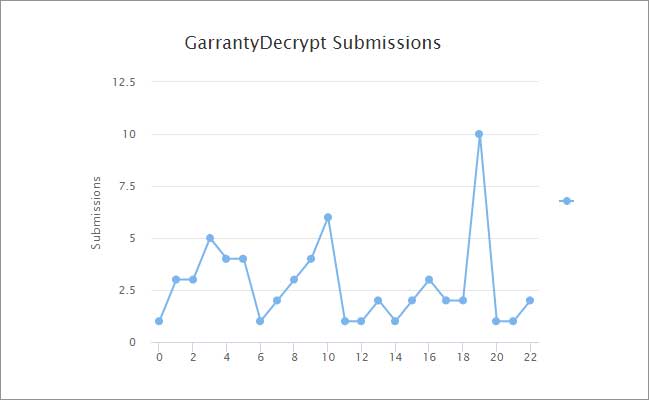
This ransomware family was found by ransomware researcher Michael Gillespie in October 2018 and while it has never achieved a large-scale distribution like other ransomware, it has seen a steady trickle of victims since it has been released.
From the submissions to ID-Ransomware, you can see a steady stream of users users submitting ransom notes or encrypted files to the service.
In a recent variant discovered once again by Gillespie in February, the developers behind GarrantyDecrypt tried a new tactic of pretending to be the security team for Proton. In this ransom note, named SECURITY-ISSUE-INFO.txt, the developers state that the victim was being attacked by an "outsider" and Proton's SECURE-SERVER service encrypted the data in order to protect it during the attack.
The developers even went as far as putting "PROTON SECURE-SERVER SYSTEMS (c) 2019" copyright statement at the bottom of the note to make it appear more legitimate.
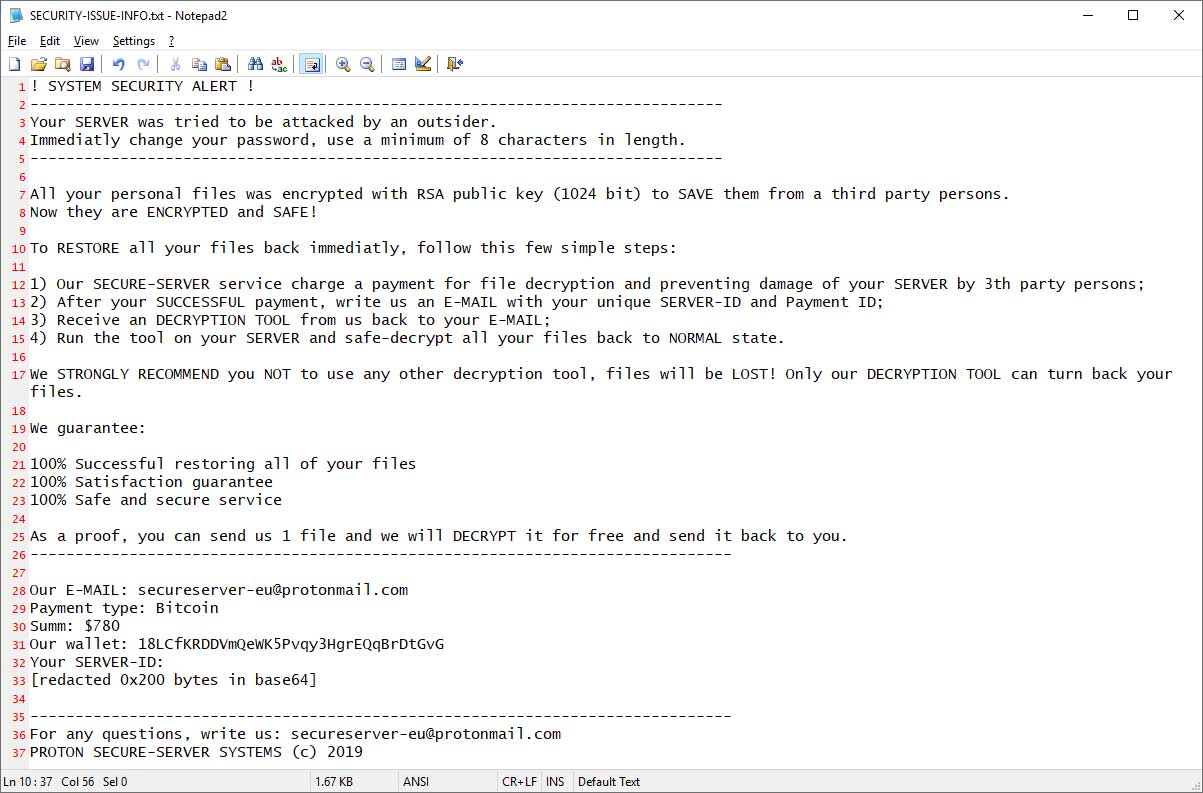
The ransom note goes on to say that Proton's SECURE-SERVER service charges a fee of $780 for securing the files during a 3rd party attack and that a victim needs to pay the fee to decrypt their files.
While I think most people would never fall for this, it is important to reiterate that this is not an email from Proton, Proton did not encrypt your data, and you are a victim of a ransomware.
Unfortunately, there is no way to decrypt this ransomware, so if you have been infected by GarrantyDecrypt you should either copy the encrypted data and a copy of the ransom note to a secure location in the hopes a key will be released in the future or try to restore from a backup.
How to protect yourself from the Ransomware
In order to protect yourself from ransomware it is important that you use good computing habits and security software. The most important step is to always have a reliable and tested backup of your data that can be restored in the case of an emergency, such as a ransomware attack.
You should also make sure that you do not have any computers running remote desktop services connected directly to the Internet. Instead place computers running remote desktop behind VPNs so that they are only accessible to those who have VPN accounts on your network.
A good security software solution that incorporates behavioral detections to combat ransomware and not just use signature detections or heuristics is important as well. For example, Emsisoft Anti-Malware and Malwarebytes Anti-Malware both contain behavioral detection that can prevent many, if not most, ransomware infections from encrypting a computer.
Last, but not least, make sure you practice the following security habits, which in many cases are the most important steps of all:
- Backup, Backup, Backup!
- Do not open attachments if you do not know who sent them.
- Do not open attachments until you confirm that the person actually sent you them,
- Scan attachments with tools like VirusTotal.
- Do not connect Remote Desktop Services directly to the Internet. Instead, make sure they can only be accessed by logging into a VPN first.
- Make sure all Windows updates are installed as soon as they come out! Also make sure you update all programs, especially Java, Flash, and Adobe Reader. Older programs contain security vulnerabilities that are commonly exploited by malware distributors. Therefore it is important to keep them updated.
- Make sure you use have some sort of security software installed that uses behavioral detections or white list technology. White listing can be a pain to train, but if your willing to stock with it, could have the biggest payoffs.
- Use hard passwords and never reuse the same password at multiple sites.
- BACKUP!
For a complete guide on ransomware protection, you visit our How to Protect and Harden a Computer against Ransomware article.
IOCs
File Names:
SECURITY-ISSUE-INFO.txt
Ransom Note Text:
! SYSTEM SECURITY ALERT !
-----------------------------------------------------------------------------
Your SERVER was tried to be attacked by an outsider.
Immediatly change your password, use a minimum of 8 characters in length.
-----------------------------------------------------------------------------
All your personal files was encrypted with RSA public key (1024 bit) to SAVE them from a third party persons.
Now they are ENCRYPTED and SAFE!
To RESTORE all your files back immediatly, follow this few simple steps:
1) Our SECURE-SERVER service charge a payment for file decryption and preventing damage of your SERVER by 3th party persons;
2) After your SUCCESSFUL payment, write us an E-MAIL with your unique SERVER-ID and Payment ID;
3) Receive an DECRYPTION TOOL from us back to your E-MAIL;
4) Run the tool on your SERVER and safe-decrypt all your files back to NORMAL state.
We STRONGLY RECOMMEND you NOT to use any other decryption tool, files will be LOST! Only our DECRYPTION TOOL can turn back your files.
We guarantee:
100% Successful restoring all of your files
100% Satisfaction guarantee
100% Safe and secure service
As a proof, you can send us 1 file and we will DECRYPT it for free and send it back to you.
------------------------------------------------------------------------------
Our E-MAIL: secureserver-eu@protonmail.com
Payment type: Bitcoin
Summ: $780
Our wallet: 18LCfKRDDVmQeWK5Pvqy3HgrEQqBrDtGvG
Your SERVER-ID:
[redacted 0x200 bytes in base64]
------------------------------------------------------------------------------
For any questions, write us: secureserver-eu@protonmail.com
PROTON SECURE-SERVER SYSTEMS (c) 2019
Associated Email addresses:
secureserver-eu@protonmail.com









Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now