
A cybercriminal using the name "salfetka" claims to be selling the source code of INC Ransom, a ransomware-as-a-service (RaaS) operation launched in August 2023.
INC has previously targeted the U.S. division of Xerox Business Solutions (XBS), Yamaha Motor Philippines, and, more recently, Scotland's National Health Service (NHS).
Simultaneously with the alleged sale, the INC Ransom operation is undergoing changes that might suggest a rift between its core team members or plans to move to a new chapter that will involve using a new encryptor.
Source code sale
The threat actor announced the sale of both the Windows and Linux/ESXi versions of INC on the Exploit and XSS hacking forums, asking for $300,000 and limiting the number of potential buyers to just three.
According to information provided to BleepingComputer by threat intelligence experts at KELA, who spotted the sale, the technical details mentioned in the forum post, such as the use of AES-128 in CTR mode and Curve25519 Donna algorithms, align with public analysis of INC Ransom samples.
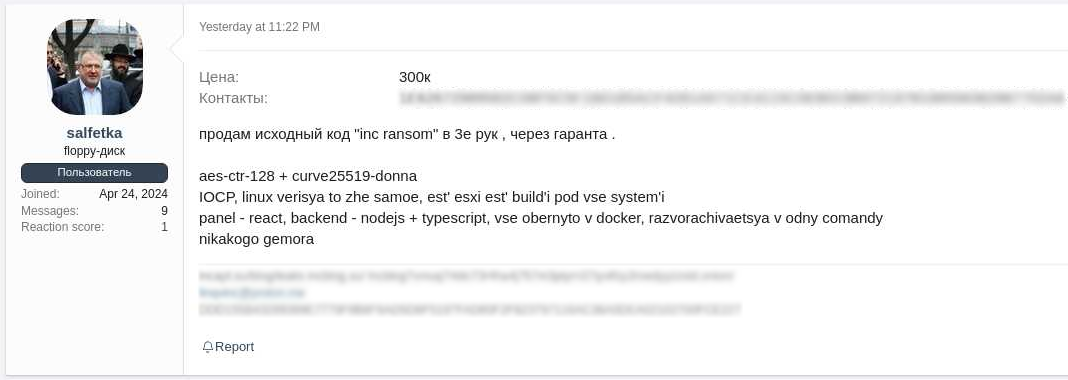
Source: KELA
KELA also told BleepingComputer that "salfetka" has been active on the hacking forums since March 2024. The threat actor was previously looking to buy network access for up to $7,000 and offered a cut to initial access brokers from ransomware attack proceeds.
Another point that adds legitimacy to the sale is "salfetka" including both the old and new INC Ransom page URLs on their signature, indicating they are affiliated with the ransomware operation.
Still, the sale could be a scam, with the threat actor carefully curating the "salfetka" account over the past few months, declaring interest in buying network access, and setting a high price tag to make the offer seem legitimate.
However, security researcher 3xp0rt told BleepingComputer that salfetka has been frequenting hacking forums and a part of ransomware gangs for some time under different aliases, including 'rinc' and 'farnetwork.'
BleepingComputer previously reported on the threat actor known as farnetwork, who was linked to numerous ransomware gangs, including Nokoyawa, JSWORM, Nefilim, Karma, and Nemty.
Currently, there are no public announcements on INC's old or new site about selling the project's source code.
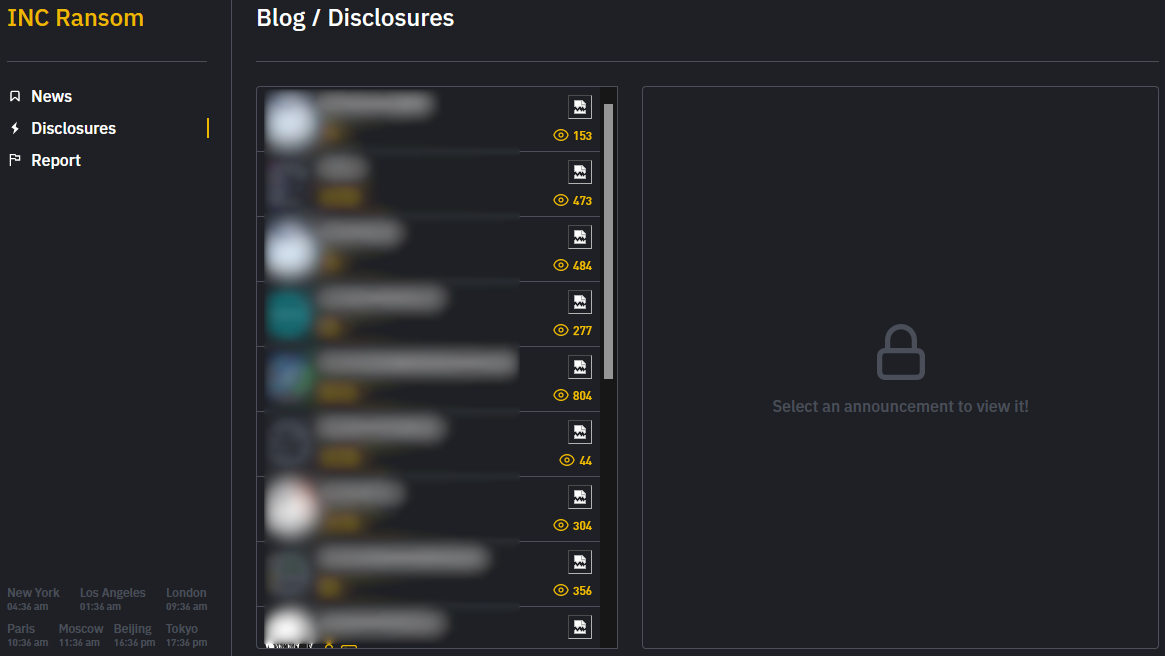
INC Ransom moving to a new site
On May 1, 2024, INC Ransom announced on its old leak site that it would move to a new data leak extortion "blog" and shared a new TOR address, stating the old site would be closed in two to three months.
.png)
Source: BleepingComputer
The new site is already up, and there's some overlap on the victims lists with the old portal, and twelve new victims not seen on the old site.
In total, the new site lists 64 victims (12 new), while the old has 91 posts, so roughly half of INC's past victims are missing.
"The discrepancies between the two sites may suggest that an operation may have experienced a leadership change or splitting into different groups," commented KELA's analysts.
"However, the fact that "salfetka" has referenced both sites as his alleged projects suggests the actor is not related to just one part of the operation."
"In this case, it is possible that the new blog was created in an attempt to gain more profits from the sale."
It is also worth noting that INC's new extortion page design visually resembles that of Hunters International, which could indicate a connection with the other RaaS operation.
Source: BleepingComputer
As opposed to a public leak that allows security analysts to crack the encryption of a ransomware strain, private source code sales of strains for which there's no available decryptor have the potential to create more trouble for organizations worldwide.
These ransomware builders are bought by highly motivated threat actors just entering the space or semi-established groups looking to up their game using a more robust and well-tested encryptor.
That is especially true when a Linux/ESXi version is on offer, which is generally more challenging to develop and costlier to acquire.
When ransomware gangs rebrand, they commonly reuse much of the source code from their old encryptors, allowing researchers to link older gangs to new operations.
Using other ransomware operation's encryptors can also help rebrand as it muddies the trail for law enforcement and researchers.
Update 5/15/24: Added information shared by security researcher 3xp0rt.









Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now