
Microsoft Outlook can be turned into a C2 beacon to remotely execute code, as demonstrated by a new red team post-exploitation framework named "Specula," released today by cybersecurity firm TrustedSec.
This C2 framework works by creating a custom Outlook Home Page using WebView by exploiting CVE-2017-11774, an Outlook security feature bypass vulnerability patched in October 2017.
"In a file-sharing attack scenario, an attacker could provide a specially crafted document file designed to exploit the vulnerability, and then convince users to open the document file and interact with the document," Microsoft says.
However, even though Microsoft patched the flaw and removed the user interface to show Outlook home pages, attackers can still create malicious home pages using Windows Registry values, even on systems where the latest Office 365 builds are installed.
As Trusted explains, Specula runs purely in Outlook's context, and it works by setting a custom Outlook home page via registry keys that call out to an interactive Python web server.
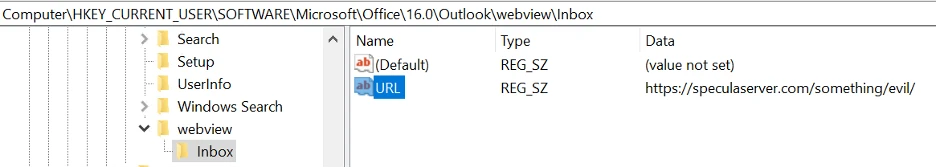
To do that, non-privileged threat actors can set a URL target in Outlook's WebView registry entries under HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Outlook\WebView\ to an external website under their control.
The attacker-controlled Outlook home page is designed to serve custom VBscript files that an attacker can use to execute arbitrary commands on compromised Windows systems.
"TrustedSec has been able to leverage this specific channel for initial access in hundreds of clients despite the existing knowledge and preventions available for this technique," TrustedSec said.
"When a custom home page is set by any of the Registry keys outlined by Microsoft in their workaround, Outlook will download and display that HTML page instead of the normal mailbox element (inbox, calendar, sent, etc.) when the associated tab is selected.
"From the downloaded HTML page we're able to run vbscript or jscript within a privileged context with more or less full access to the local system as if we were running cscript / wscript.exe."
While a device first needs to be compromised to configure the Outlook Registry entry, once configured, attackers can use this technique for persistence and to spread laterally to other systems.
Since outlook.exe is a trusted process, it makes it easier for attackers to evade existing software as commands are executed.
As U.S. Cyber Command (US CyberCom) warned five years ago, the CVE-2017-11774 Outlook vulnerability was also used to target U.S. government agencies.
Security researchers from Chronicle, FireEye, and Palo Alto Networks later linked these attacks to the Iranian-sponsored APT33 cyber espionage group.
"FireEye first observed APT34 use CVE-2017-11774 in June 2018, followed by adoption by APT33 for a significantly broader campaign beginning in July 2018 and continuing for at least a year," FireEye cybersecurity researchers said at the time.









Comments
scpcguy - 3 months ago
How about preemptively creating the "Webview" key and then setting its permissions to Administrators only as a mitigation?
MegasChara - 3 months ago
Does the "Block Office communication application from creating child processes" and "Block all Office applications from creating child processes" Intune ASR rules block wscript from launching payloads despite this Outlook vuln? That would mitigate a large amount of damage this could cause.