
Almost every week we add another workflow to our automation library. Our platform and copilot are helping people automate otherwise tedious tasks in security operations. Integrations between platforms traditionally involved security engineers writing custom code using application programming interfaces (APIs).
For example, if you wanted to scan all your S3 buckets for public access, looking for READ and WRITE permissions, and send a notification to an incident response Slack channel, you would need Python or Bash code with many API calls.
However, with security automation platforms like Blink Ops, this has drastically changed. You can integrate automation into your environment by writing a simple prompt, and the copilot will build the workflow it thinks you need. It's then a matter of entering a few parameters and adding authentication credentials. This can save people in security operations hundreds of hours a year.
Listed below are five incident response/security operations workflows you can automate with Blink Ops. These examples give you an idea of how Blink Ops automations can speed up your work.
1. Monitoring for Subdomain Takeover with AWS and Wiz
Subdomain takeover occurs when a DNS entry points to a nonexistent or inactive resource, allowing attackers to hijack the domain. Trying to prevent this manually involves frequent checks to ensure all DNS configurations are correct.
This process is completely automated using Blink Ops. In conjunction with AWS Route 53, Blink Ops scans for orphaned/dangling CNAME records pointing to resources that no longer exist using Wiz. Upon detection of issues, Blink Ops sends an immediate alert to a designated Slack channel describing the misconfigured DNS entry.
Wiz then quarantines the record or takes remediation steps. When no issues are found, a notification is sent that everything is secure. This automation simplifies detection and mitigation of subdomain takeover risks.
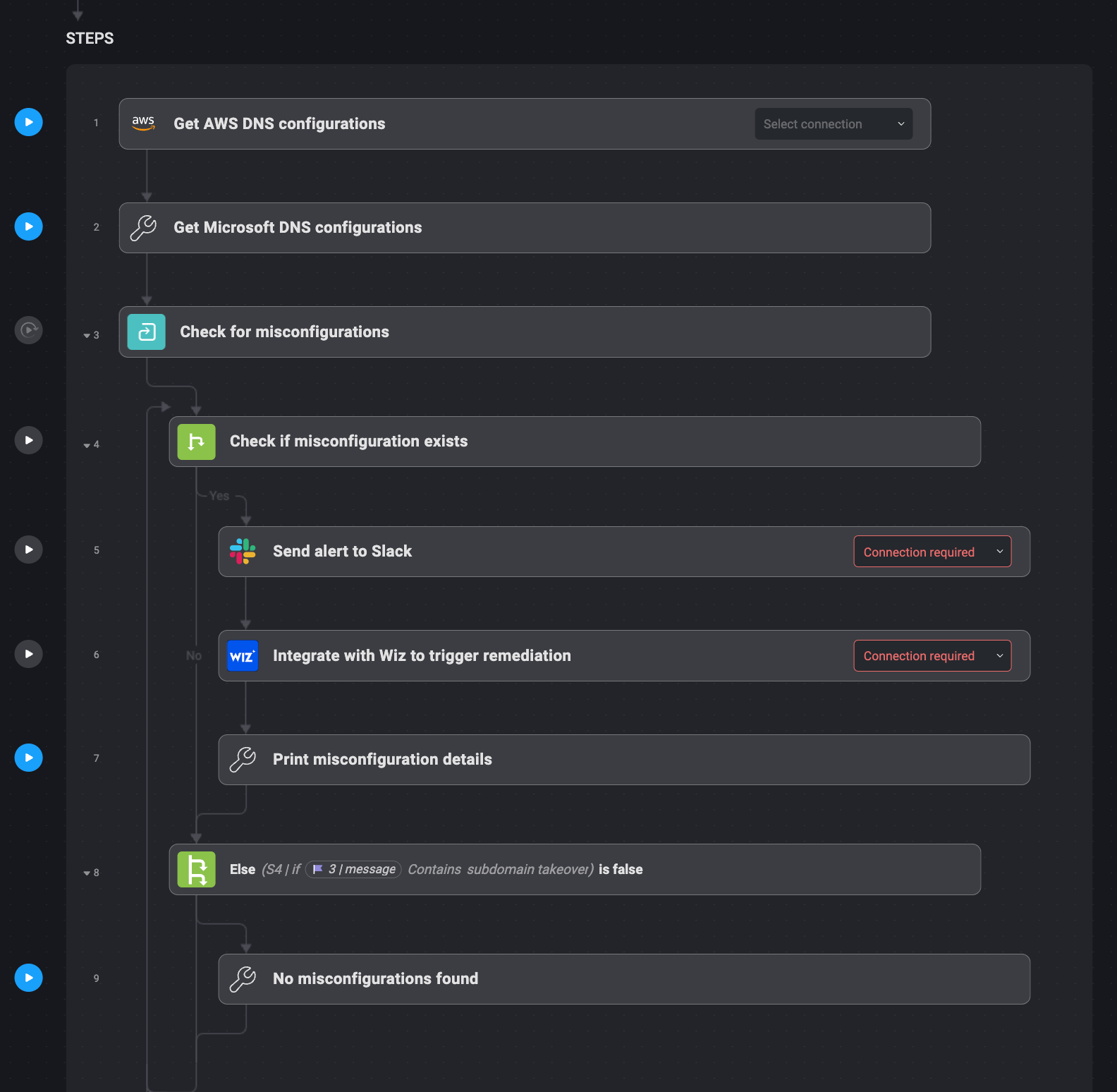
Bullet-Point Steps:
1. For DNS configurations, Blink Ops connects to AWS Route 53.
2. Wiz checks DNS entries for dangling orphaned CNAME records.
3. When a vulnerable record is found, Blink Ops sends an alert to Slack.
4. Wiz either quarantines the record or applies the fix.
5. If no problems are found, a confirmation email is sent confirming this.
2. Monitoring for Exposed S3 Buckets with Slack Alerts
Exposed S3 buckets are a significant security risk for any organization, and tracking them manually every day can be tedious. You could address this by enabling daily automatic scans of S3 buckets with public READ permissions.
This workflow integrates with AWS S3, and Blink Ops can scan each bucket marked for public access. Detecting a bucket with public READ access triggers a Slack alert from Blink Ops, giving the security team information about the bucket — including its name and permissions.
A follow-up action by Blink Ops can also remove the public permission for the bucket. This workflow identifies exposed buckets quickly and appropriately so that sensitive data is not exposed to unauthorized users.
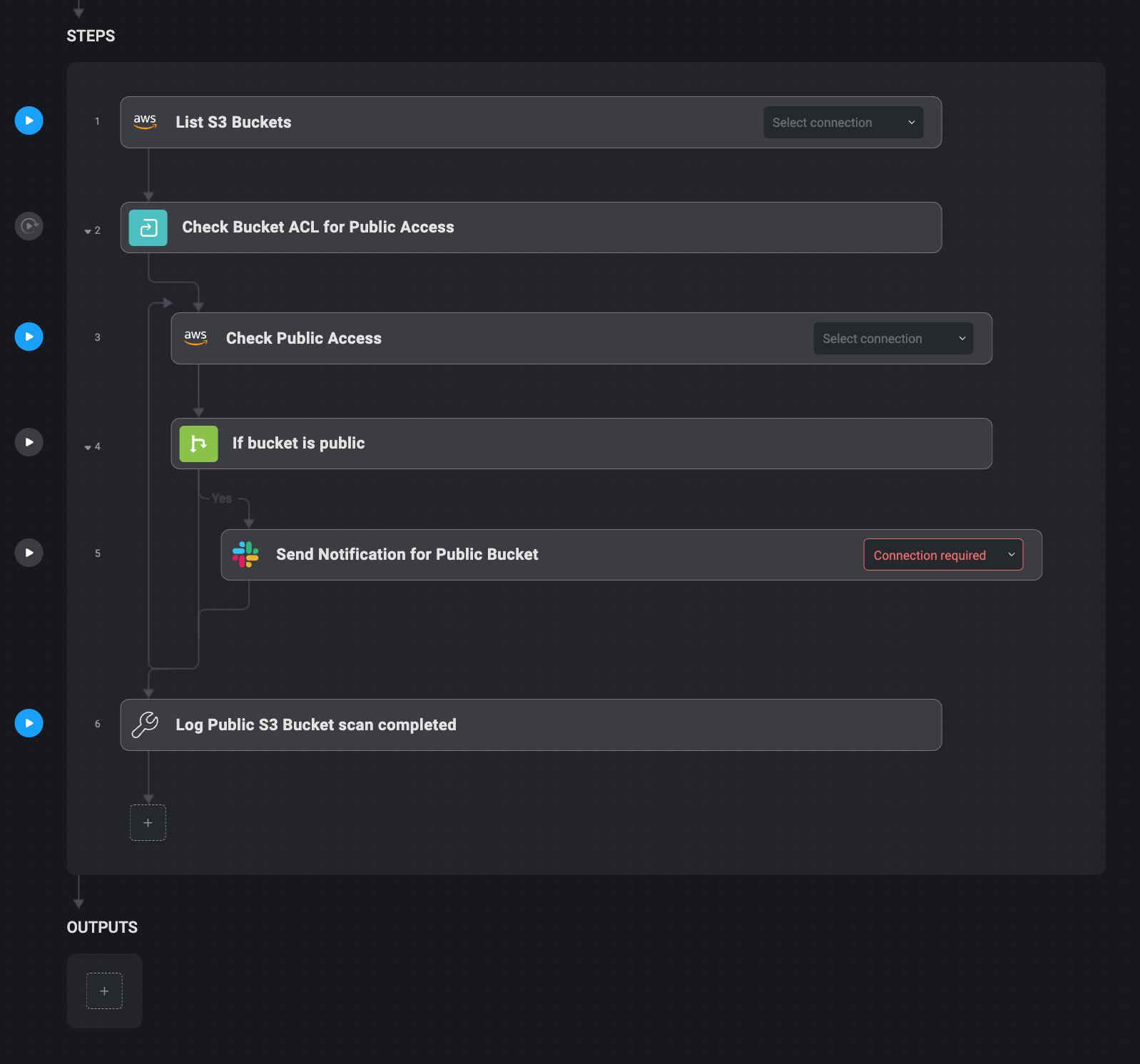
Bullet-Point Steps:
1. Daily, Blink Ops checks AWS S3 buckets for public read permissions.
2. Any bucket found with public READ access triggers a Slack alert.
3. Blink Ops can optionally revoke READ permissions (note - not included above).
4. The bucket is secured, and the security team is notified.
3. Responding to Failed EC2 Logins and Privilege Escalation
Failed login attempts and unauthorized privilege escalation detection and response on EC2 instances are critical to security. Blink Ops can automate this so that threats are detected in real-time and responded to.
You can monitor EC2 instances to reveal repeated failed SSH or RDP login attempts—five or more failed attempts in a 15-minute window—via Slack. You can also track privilege escalation by monitoring IAM role changes, like when an EC2 instance is granted additional privileges like AdminAccess.
When this happens, Blink Ops takes a snapshot of the affected EC2 instance for forensic analysis and sends an alert to the security team describing what happened. This automation relieves security teams of manual log monitoring during login failures or privilege abuse.
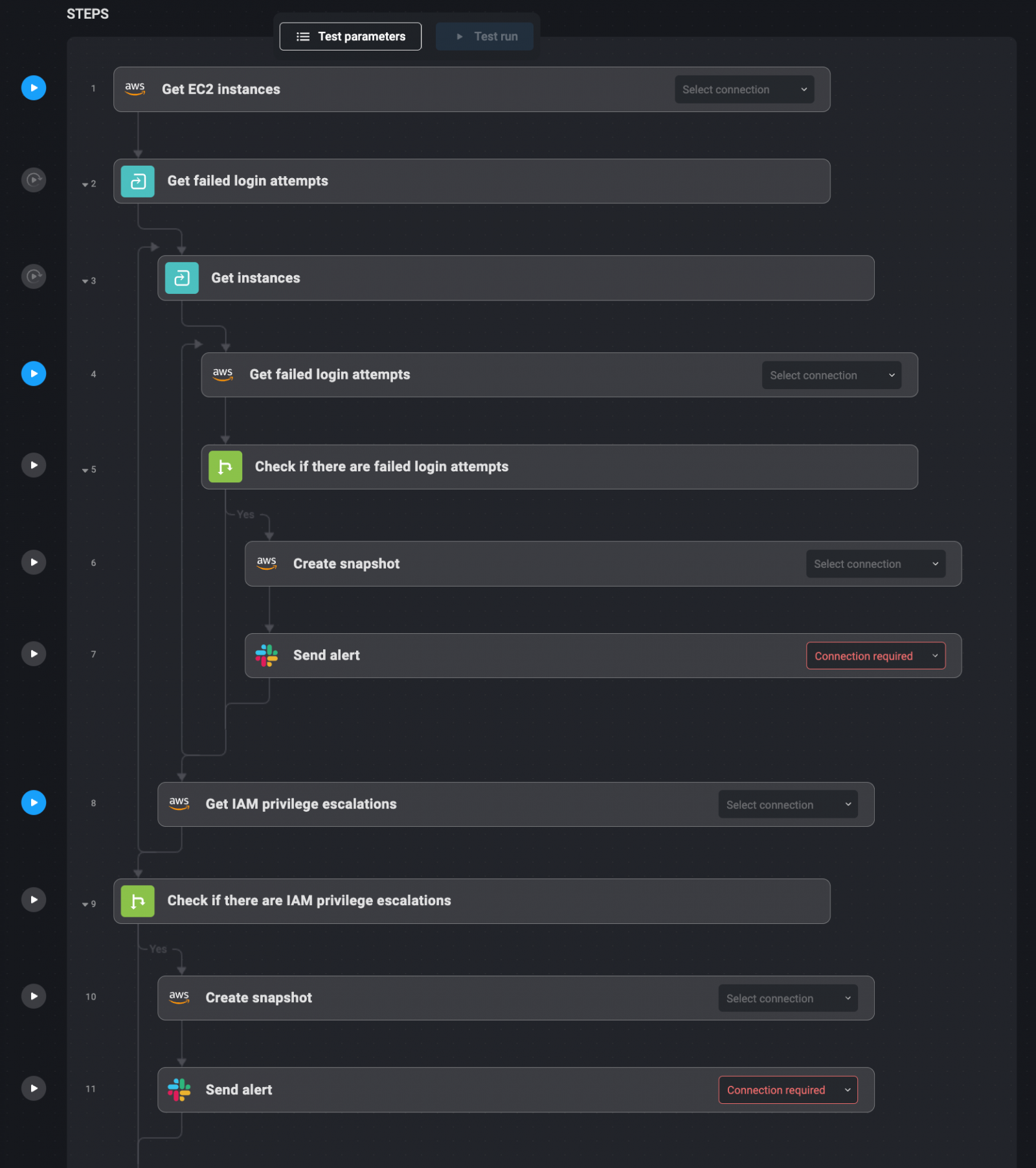
Bullet-Point Steps:
1. Failed SSH and RDP login attempts on EC2 instances are tracked by Blink Ops.
2. If > 5 failed logins occur within 15 minutes, Blink Ops issues a Slack alert.
3. IAM role changes such as privilege escalation are also tracked by Blink Ops.
4. When privilege escalation occurs, Blink Ops takes a snapshot.
5. Security teams receive alerts with all relevant details about the event.
4. Vulnerability Detection and Alerting with AWS Inspector
Vulnerability management is essential for keeping cloud environments secure. Blink Ops simplifies the process by integrating with AWS Inspector to automatically scan EC2 instances and containers for critical vulnerabilities.
As part of Blink Ops, AWS Inspector can check for high-severity vulnerabilities such as CVSS scores greater than 7. Once a critical vulnerability is detected, Blink Ops notifies the designated Slack channel of the vulnerable instance/container. The alert also links to a remediation guide or playbook for manual intervention.
For vulnerabilities that cannot be automatically patched, Blink Ops logs the details and allows for manual remediation by a security engineer. Once the remediation is complete, Wiz verifies that the vulnerability has been fixed, ensuring that the cloud environment is secure.
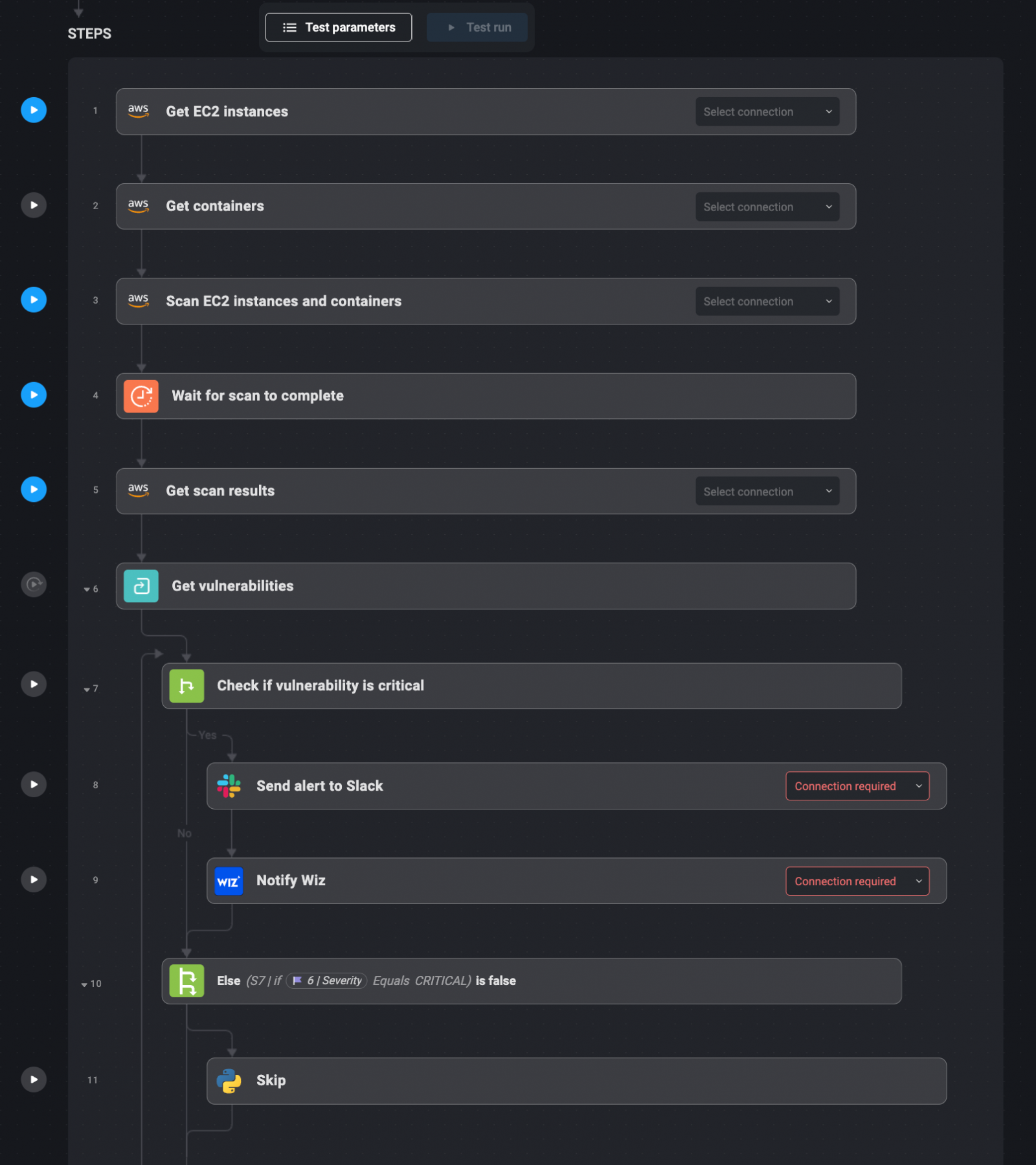
Bullet-Point Steps:
1. AWS Inspector scans EC2 instances and containers for vulnerabilities.
2. Upon discovery of a vulnerability (CVSS >7), Blink Ops sends an alert to Slack.
3. Wiz confirms that the vulnerability was fixed after manual remediation.
4. Security teams are notified of the fix and verification process completion.
5. Automating S3 Encryption Enforcement with AWS and Wiz
Securing sensitive data in S3 buckets is best practice. This is solved by automating S3 bucket monitoring for encryption compliance with Blink Ops.
Monitoring of sensitive-data tagged S3 buckets via Blink Ops is integrated with AWS Config. It verifies that such buckets are encrypted with AES-256. Upon detection of an unencrypted bucket, Blink Ops applies AES-256 encryption using AWS's PutBucketEncryption API.
After encryption has been applied, Blink Ops sends a Slack confirmation of the update, and Wiz is triggered to verify that encryption was applied. Such an automated workflow protects all sensitive data without any human intervention and enables security teams to enforce encryption policies across the cloud environment.
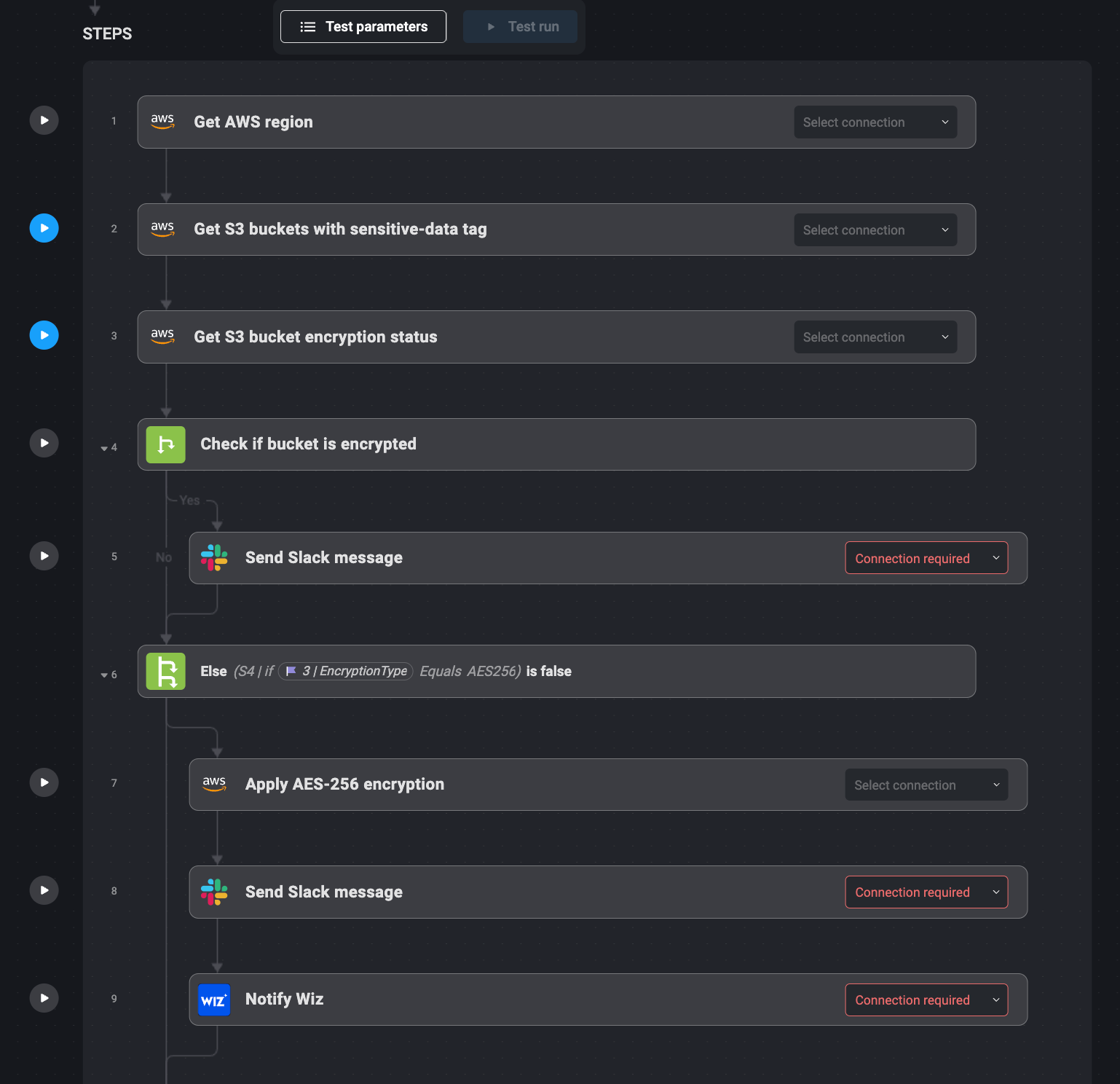
Bullet-Point Steps:
1. AWS Config tracks sensitive-data tagged S3 buckets monitored by Blink Ops.
2. If unencrypted, Blink Ops triggers AWS to apply encryption.
3. When encryption is applied, Slack notification is sent.
4. Wiz confirms the encryption has been applied correctly.
5. Security teams now know the bucket is secured.
Take Your Next Steps With Blink Ops
The use cases above are just some of the many possibilities that Blink Ops can automate for you. Blink Ops can be used with platforms like AWS and Wiz to automate processes that used to require custom code and manual labor. This means security teams can save hours, respond faster to threats, and reduce human error risk.
Automate time-consuming tasks so your team can focus on higher-value security initiatives—using Blink Ops. Whether you need to monitor for subdomain takeover, detect failed EC2 logins, or automate vulnerability scans, Blink Ops lets you optimize and scale your security operations.
Get started with Blink Ops today to automate repetitive tasks.
Sponsored and written by Blink Ops.








Comments have been disabled for this article.