
An emerging phishing-as-a-service (PhaaS) platform called Mamba 2FA has been observed targeting Microsoft 365 accounts in AiTM attacks using well-crafted login pages.
Additionally, Mamba 2FA offers threat actors an adversary-in-the-middle (AiTM) mechanism to capture the victim's authentication tokens and bypass multi-factor authentication (MFA) protections on their accounts.
Mamba 2FA is currently sold to cybercriminals for $250/month, which is a competitive price that positions it among the most alluring and fastest-growing phishing platforms in the space.
Discovery and evolution
Mamba 2FA was first documented by Any.Run analysts in late June 2024, but Sekoia reports that it has been tracking activity linked to the phishing platform since May 2024.
Additional evidence shows that Mamba 2FA has been supporting phishing campaigns since November 2023, with the kit being sold on ICQ and later on Telegram.
Following Any.Run's report of a campaign backed by Mamba 2FA, the operators of the phishing kit made several changes to their infrastructure and methods to increase the stealthiness and longevity of the phishing campaigns.
For example, starting in October, Mamba 2FA introduced proxy servers sourced from IPRoyal, a commercial provider, to mask the IP addresses of relay servers on authentication logs.
Previously, relay servers connected directly to Microsoft Entra ID servers, exposing the IP addresses and making blocks easier.
Link domains used in phishing URLs are now very short-lived and typically rotated weekly to avoid blocklisting by security solutions.
Another change was enhancing HTML attachments used in phishing campaigns with benign filler content to hide a small snippet of JavaScript that triggers the attack, making it harder for security tools to detect.
"Biting" Microsoft 365 users
Mamba 2FA is specifically designed to target users of Microsoft 365 services, including corporate and consumer accounts.
Like other similar PhaaS platforms, it uses proxy relays to conduct AiTM phishing attacks, allowing the threat actors to access one-time passcodes and authentication cookies.
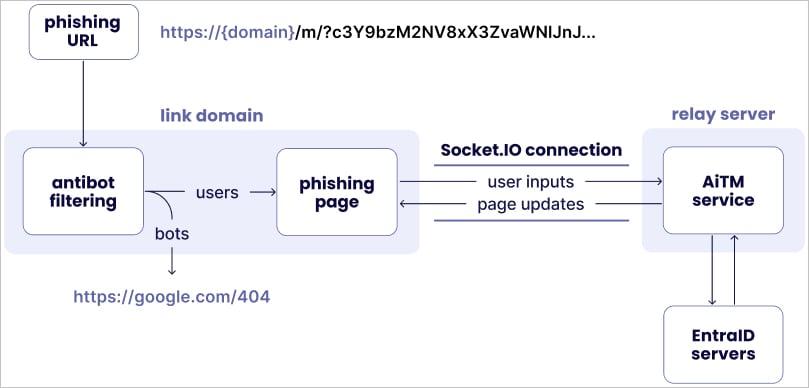
The AiTM mechanism uses the Socket.IO JavaScript library to establish communication between the phishing page and the relay servers at the backend, which in turn communicate with Microsoft's servers using the stolen data.
Source: Sekoia
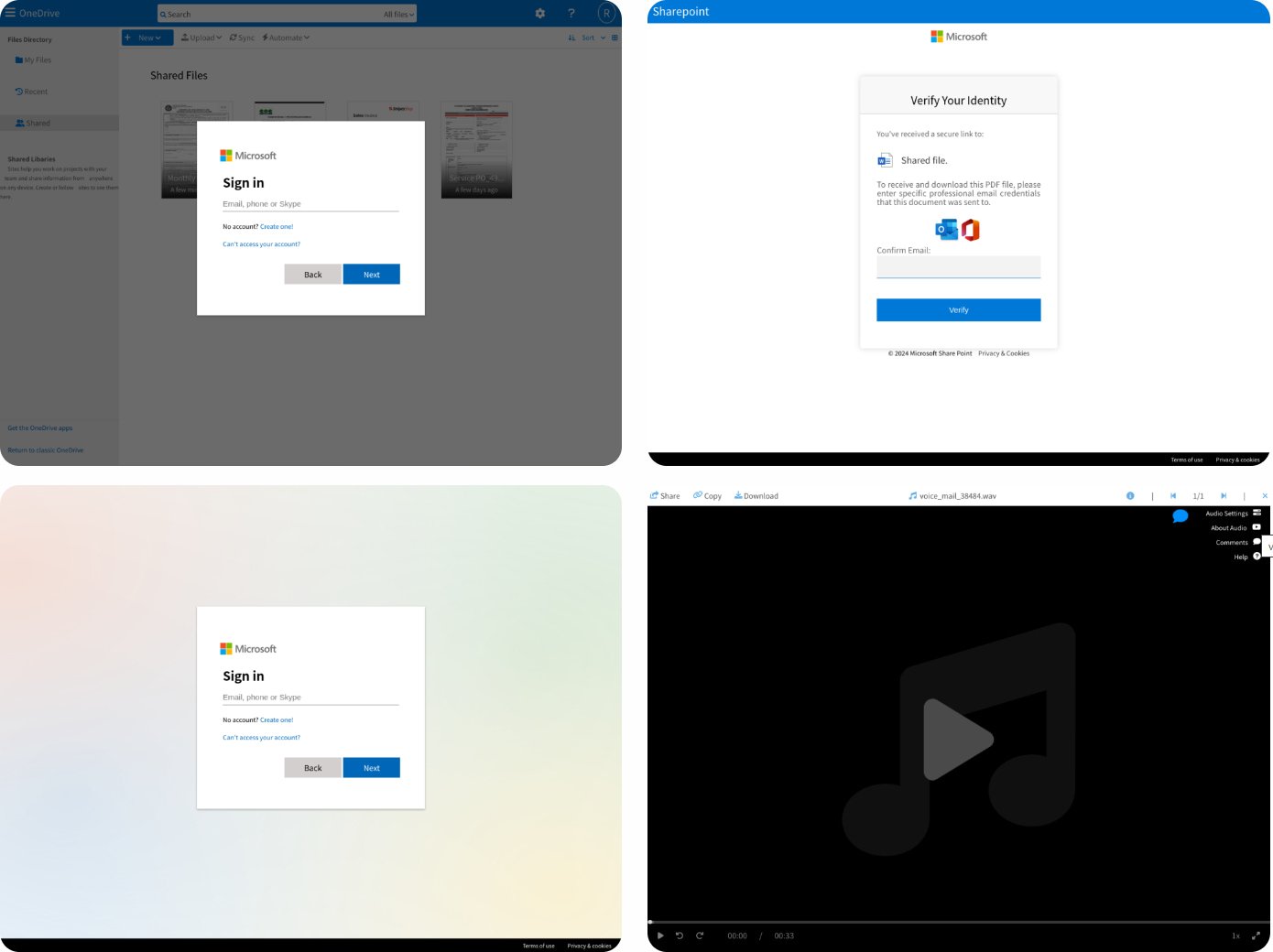
Mamba 2FA offers phishing templates for various Microsoft 365 services, including OneDrive, SharePoint Online, generic Microsoft sign-in pages, and fake voicemail notifications that redirect to a Microsoft login page.
For enterprise accounts, the phishing pages dynamically assume the targeted organization's custom login branding, including logos and background images, making the attempt appear more authentic.
Source: Sekoia
Captured credentials and authentication cookies are transmitted to the attacker through a Telegram bot, enabling them to initiate a session immediately.
Mamba 2FA also features sandbox detection, redirecting users to Google 404 webpages when it deduces it's being under analysis.
Overall, the Mamba 2FA platform is yet another threat to organizations, allowing low-skilled actors to perform highly effective phishing attacks.
To protect against PhaaS operations using AiTM tactics, consider using hardware security keys, certificate-based authentication, geo-blocking, IP allowlisting, device allowlisting, and token lifespan shortening.









Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now