Intel has fixed a high-severity CPU vulnerability in its modern desktop, server, mobile, and embedded CPUs, including the latest Alder Lake, Raptor Lake, and Sapphire Rapids microarchitectures.
Attackers can exploit the flaw—tracked as CVE-2023-23583 and described as a 'Redundant Prefix Issue'—to escalate privileges, gain access to sensitive information, or trigger a denial of service state (something that could prove very costly for cloud providers).
"Under certain microarchitectural conditions, Intel has identified cases where execution of an instruction (REP MOVSB) encoded with a redundant REX prefix may result in unpredictable system behavior resulting in a system crash/hang, or, in some limited scenarios, may allow escalation of privilege (EoP) from CPL3 to CPL0," Intel said.
"Intel does not expect this issue to be encountered by any non-malicious real-world software. Redundant REX prefixes are not expected to be present in code nor generated by compilers. Malicious exploitation of this issue requires execution of arbitrary code. Intel identified the potential for escalation of privilege in limited scenarios as part of our internal security validation in a controlled Intel lab environment."
Specific systems with affected processors, including those with Alder Lake, Raptor Lake, and Sapphire Rapids, have already received updated microcodes before November 2023, with no performance impact observed or expected issues.
The company also released microcode updates to address the issue for the other CPUs, with users advised to update their BIOS, system OS, and drivers to receive the latest microcode from their original equipment manufacturer (OEM), operating system vendor (OSV), and hypervisor vendors.
The complete list of Intel CPUs affected by the CVE-2023-23583 vulnerability and mitigation guidance are available here.
"Intel discovered this issue internally and was already preparing the ecosystem to release a mitigation through our well-documented Intel Platform Update process," an Intel spokesperson told BleepingComputer.
"At the request of customers, including OEMs and CSPs, this process typically includes a validation, integration, and deployment window after Intel deems the patch meets production quality, and helps ensure that mitigations are available to all customers on all supported Intel platforms when the issue is publicly disclosed.
"While Intel is not aware of any active attacks using this vulnerability, affected platforms have an available mitigation via a microcode update."
Reptar is a 'very strange' vulnerability
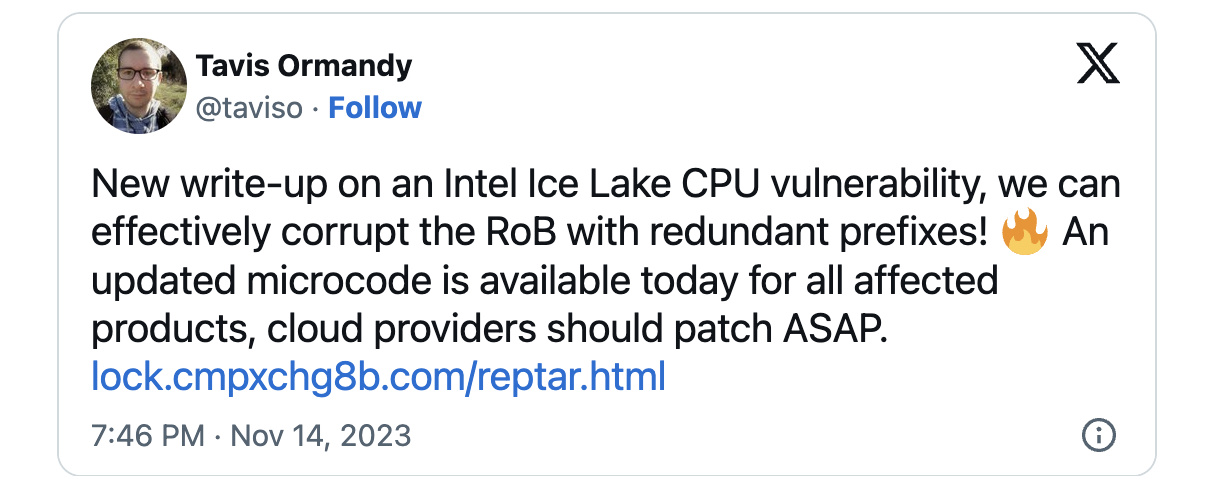
Google vulnerability researcher Tavis Ormandy revealed today that this security bug was also independently discovered by multiple research teams within Google, including Google Information Security Engineering and the silifuzz team, who dubbed it Reptar.
As Google Cloud VP and CISO Phil Venables explained today, the vulnerability is related to "how redundant prefixes are interpreted by the CPU which leads to bypassing the CPU's security boundaries if exploited successfully."
While, commonly, redundant prefixes should be ignored, they're triggering "very strange behavior" because of this vulnerability, as discovered by Ormandy during testing.
"We observed some very strange behavior while testing. For example, branches to unexpected locations, unconditional branches being ignored and the processor no longer accurately recording the instruction pointer in xsave or call instructions," Ormandy said.
"This already seemed like it could be indicative of a serious problem, but within a few days of experimenting we found that when multiple cores were triggering the same bug, the processor would begin to report machine check exceptions and halt."
Earlier this year, Google security researchers discovered the Downfall vulnerability impacting modern Intel CPUs and the Zenbleed flaw, which lets attackers steal sensitive data like passwords and encryption keys from systems with AMD Zen2 CPUs.
Today, AMD also patched a vulnerability called CacheWarp that lets malicious actors hack AMD SEV-protected VMs to escalate privileges and gain remote code execution.
Update: Added Intel statement.









Comments
ZeroYourHero - 1 year ago
Would be nice if processor updates could be installed securely without the motherboard manufacturer being involved in the process.