
The Toronto Public Library is experiencing ongoing technical outages due to a Black Basta ransomware attack.
The Toronto Public Library (TPL) is Canada's largest public library system, giving access to 12 million books through 100 branch libraries across the city. The library system has 1,200,000 registered members and operates on a budget that surpasses $200M.
Earlier this week, TPL warned that a cyberattack is causing technical outages on its websites and some online services.
These outages include the tpl.ca site being taken offline, the inability to access your online account, and outages in the tpl:map passes and digital collections services.
The library warned that public computers and printing services are also unavailable.
The Toronto Public Library says that there is no evidence that the personal information of staff or customers has been compromised and that they are actively investigating the incident with law enforcement and third-party cybersecurity experts.
"TPL has proactively prepared for cybersecurity issues and promptly initiated measures to mitigate potential impacts," reads a notice on a temporary library website hosted on Typepad.
"We have engaged with third-party cybersecurity experts to help us in resolving this situation. We do anticipate though that it may take several days before all systems are fully restored to normal operations."
Do you have information about this or another ransomware attack? If you want to share the information, you can contact us securely and confidentially on Signal at +1 (646) 961-3731, via email at lawrence.abrams@bleepingcomputer.com, or by using our tips form.
Black Basta ransomware behind attack on TPL
BleepingComputer has since learned that the Black Basta ransomware operation is behind the attack on the Toronto Public Library.
A photo of the ransom note shared with BleepingComputer allowed us to confirm that the ransomware operation was behind the attack.
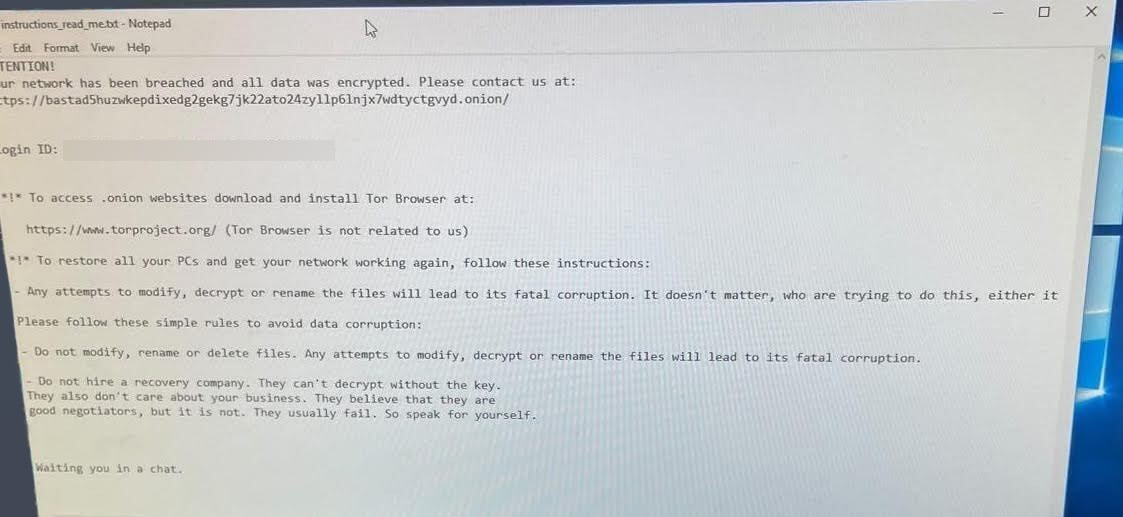
Source: BleepingComputer
According to a TPL employee, the attack occurred overnight on October 27th, impacting numerous services Saturday morning.
BleepingComputer was told that the attack did not impact phones and had limited impact on email, with those logged into their Office 365 accounts still able to access them. However, employees who were not currently logged into email were no longer able to access the system.
All other internal systems were shut down after the attack as a precaution to prevent the spread of the malware.
We were told the organization's main servers containing sensitive data were not encrypted, potentially meaning that the threat actors did not have full access to the organization's networks and data.
While it is unknown now if the ransomware gang stole data during the attack, data theft is a significant component of their extortion strategy.
We will learn if data was stolen if the threat actors will use it as leverage to pressure TPL into paying a ransom.
Who is Black Basta?
The Black Basta ransomware gang launched its ransomware operation in April 2022 and quickly began targeting corporate victims in double-extortion attacks.
One of its first attacks was against the American Dental Association, during which the threat actors leaked stolen data.
By June 2022, Black Basta had partnered with the QBot malware operation to drop Cobalt Strike beacons on infected devices for initial access to corporate networks.
Once they gained access to a network, they would steal credentials and spread laterally throughout a network while stealing data.
After all data is stolen and the hackers gain access to the Windows domain controller, the threat actors deploy an encryptor throughout the network to encrypt devices.
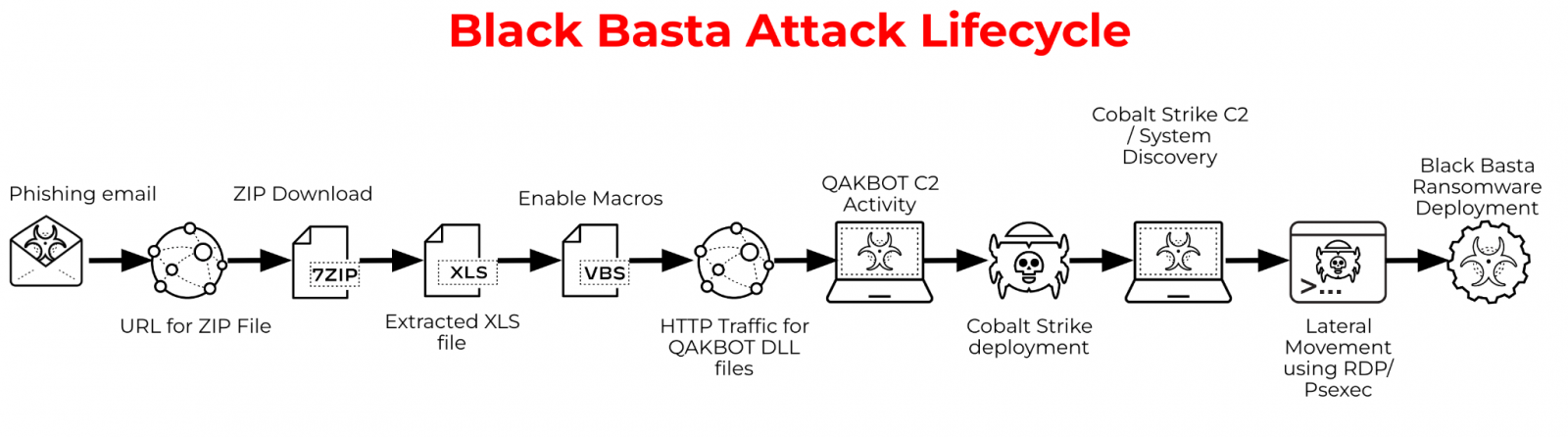
Source: Palo Alto Networks Unit 42
Like almost all ransomware operations, Black Basta utilizes a Linux encryptor to target VMware ESXi virtual machines running on Linux servers.
In June 2022, the Conti ransomware operation shut down after suffering a series of embarrassing data breaches. Researchers believe that the cybercrime syndicate splintered into smaller groups, with one of them believed to be Black Basta.
However, other researchers believe there is a link between Black Basta and the Fin7 cybercrime operation, a financially motivated cybercrime gang also known as Carbanak.
Since its launch, the threat actors have been responsible for a stream of attacks, including Capita, Sobeys, Knauf, and Yellow Pages Canada.
Recently, the ransomware operation attacked ABB, a Swiss tech multinational and U.S. government contractor, and leaked the company's stolen data.









Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now