
Threat researchers have found a new feature-rich malware that can encrypt files on any system running PHP, making it a high risk for Windows, macOS, and Linux web servers.
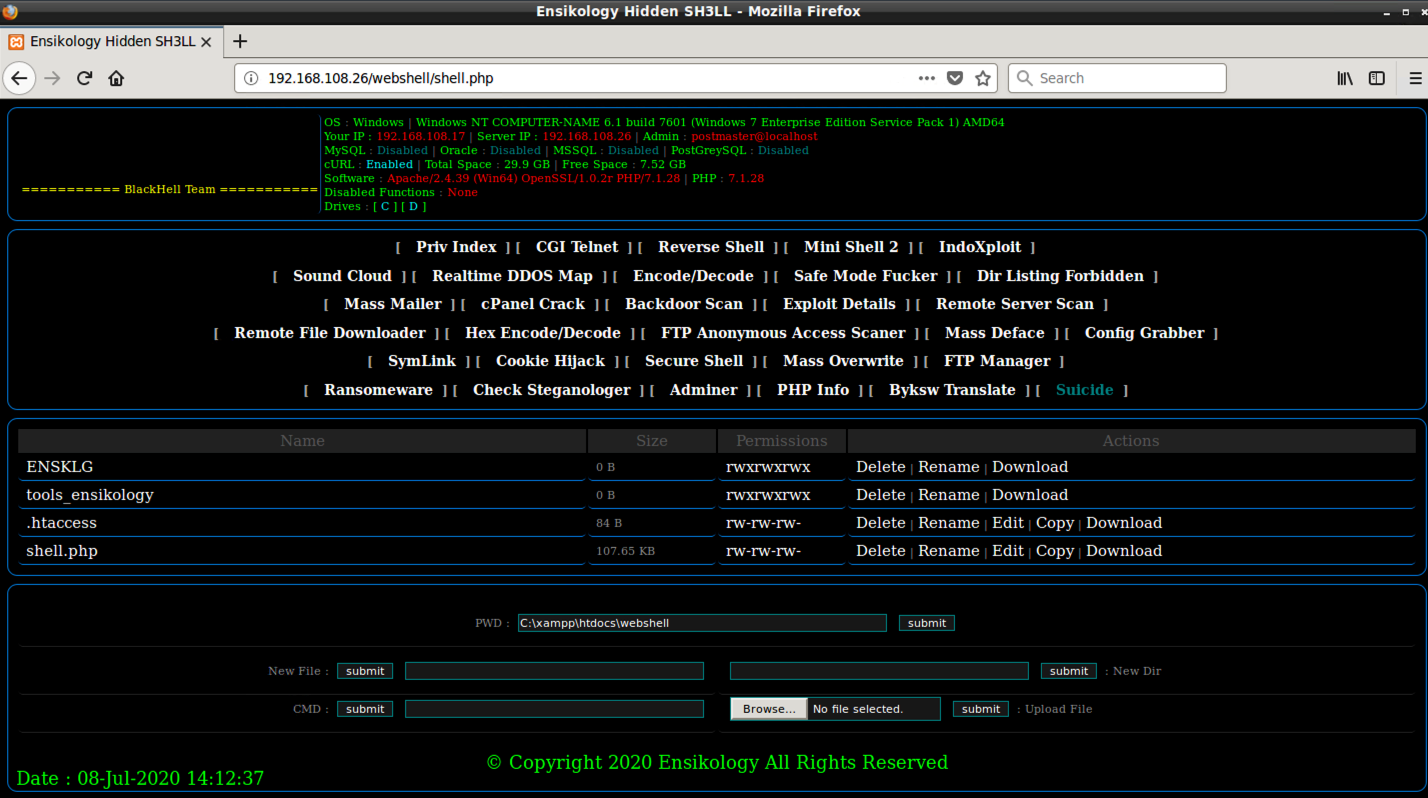
The malware received the name Ensiko and is a web shell written in PHP. Attackers can use it to remotely control a compromised system and run a host of malicious activities.
Variety of options
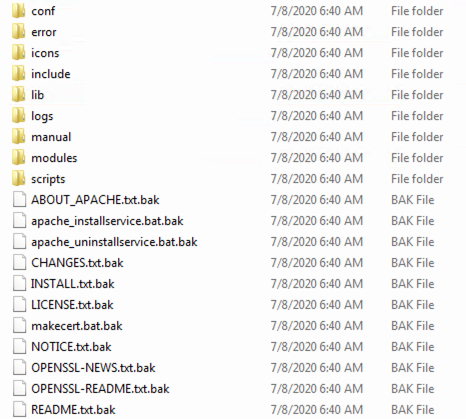
From Ensiko’s large list of capabilities, the file-encryption component stands out as it can be used for ransomware attacks against servers.
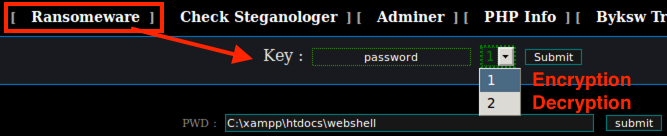
Researchers at Trend Micro analyzed the malware and found that it uses the symmetric Rijnadel-128 cipher in CBC mode to encrypt files. Below is the code responsible for locking and unlocking the data:

Ensiko encrypts files in a web shell directory and subdirectories and appends the .BAK extension to processed files.
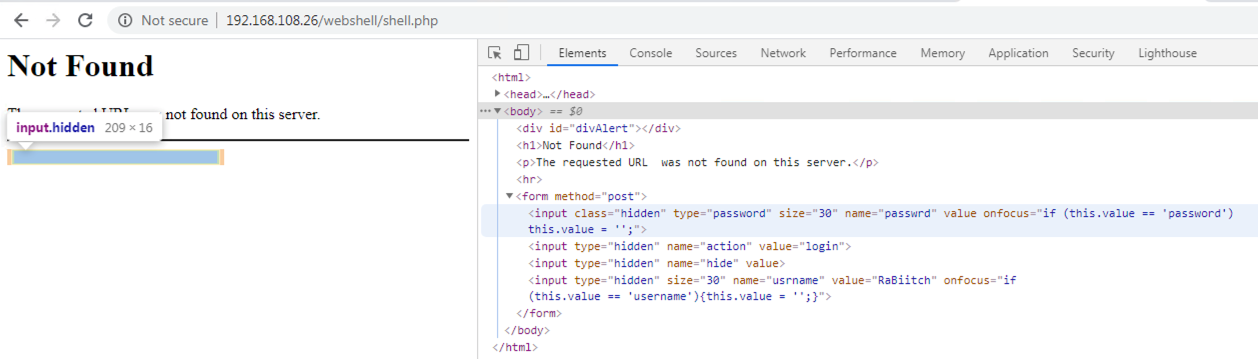
The researchers found that the malware can be password protected for secure access and avoid a takeover like it happened last week with Emotet when someone replaced the malware payloads with memes.
Authenticating to this web shell is not straightforward. The developer hid the login form on a “Not Found” page. For the analyzed sample, the access key is “RaBiitch.”
To expand capabilities, Ensiko can load several tools, which the malware downloads from Pastebin and stores them in a directory named “tools_ensikology.”
One of the functions of the malware is called Steganologer, which can identify image files that have code in their metadata (EXIF headers). The code is then extracted and executed on the compromised server.
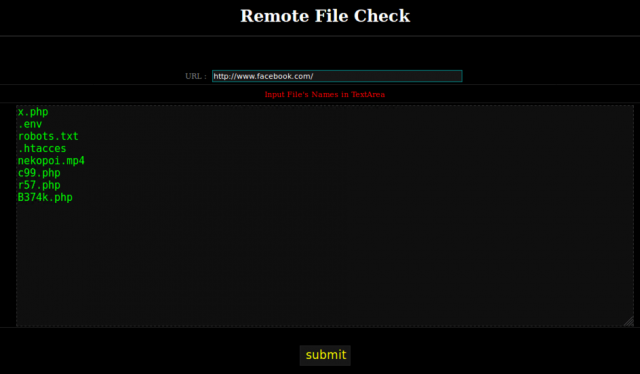
Trend Micro malware analyst Aliakbar Zahravi discovered that Ensiko can also check if a web shell from a predefined list is present on a remote host. Another scanning function called Remote File Check allows the operator to look for arbitrary files on a remote system.
Another function in this malicious tool allows recursive overwrite of all files with a specified extension in a directory of a web shell.
Ensiko’s capabilities do not stop at this, though. The malware lets threat actors run brute-force attacks on FTP, cPanel, and Telnet, thus enabling them extended access.
You can see in the image below what Ensiko web shell provides, as well as a complete list of features compiled by Zahravi:
| Features | Description |
| Priv Index | Download ensikology.php from pastebin |
| Ransomeware | Encrypt files using RIJNDAEL 128 with CBC mode |
| CGI Telnet | Download CGI-telnet version 1.3 from pastebin;
CGI-Telnet is a CGI script that allows you to execute commands on your web server. |
| Reverse Shell | PHP Reverse shell |
| Mini Shell 2 | Drop Mini Shell 2 webshell payload in ./tools_ensikology/ |
| IndoXploit | Drop IndoXploit webshell payload in ./tools_ensikology/ |
| Sound Cloud | Display sound cloud |
| Realtime DDOS Map | Fortinet DDoS map |
| Encode/Decode | Encode/decode string buffer |
| Safe Mode Fucker | Disable PHP Safe Mode |
| Dir Listing Forbidden | Turn off directory indexes |
| Mass Mailer | Mail Bombing |
| cPanel Crack | Brute-force cPanel, ftp, and telnet |
| Backdoor Scan | Check remote server for existing web shell |
| Exploit Details | Display system information and versioning |
| Remote Server Scan | Check remote server for existing web shell |
| Remote File Downloader | Download file from remote server via CURL or wget |
| Hex Encode/Decode | Hex Encode/Decode |
| FTP Anonymous Access Scaner | Search for Anonymous FTP |
| Mass Deface | Defacement |
| Config Grabber | Grab system configuration such as “/etc/passwd” |
| SymLink | link |
| Cookie Hijack | Session hijacking |
| Secure Shell | SSH Shell |
| Mass Overwrite | Rewrite or append data to the specified file type. |
| FTP Manager | FTP Manager |
| Check Steganologer | Detects images with EXIF header |
| Adminer | Download Adminer PHP database management into the ./tools_ensikology/ |
| PHP Info | Information about PHP’s configuration |
| Byksw Translate | Character replacement |
| Suicide | Self-delete |









Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now