
A darknet platform dubbed 'Zombinder' allows threat actors to bind malware to legitimate Android apps, causing victims to infect themselves while still having the full functionality of the original app to evade suspicion.
This new platform was discovered by cybersecurity firm ThreatFabric, which spotted malicious Windows and Android campaigns distributing multiple malware families.
The campaign impersonates Wi-Fi authorization portals, supposedly helping users to access internet points as a lure to push various malware families. The site then prompts a user to download either a Windows or Adware version of the application, which in reality, is malware.
ThreatFabric reports that the operation has claimed thousands of victims, with Erbium stealer infections alone having stolen data from 1,300 different computers.

Zombinder for Android
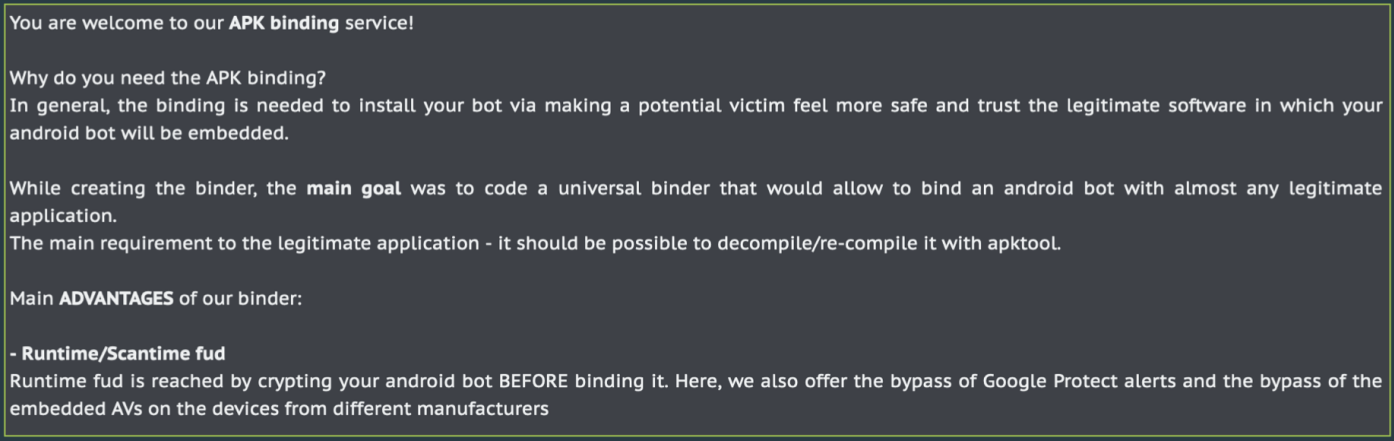
An interesting aspect of the campaign is the darknet service, which the researchers dubbed “Zombinder,” which offers malicious APK binding of malware to legitimate Android applications.
Zombinder launched in March 2022 as a malware packer on APK files, and according to ThreatFabric, it is now growing popular in the cybercrime community.
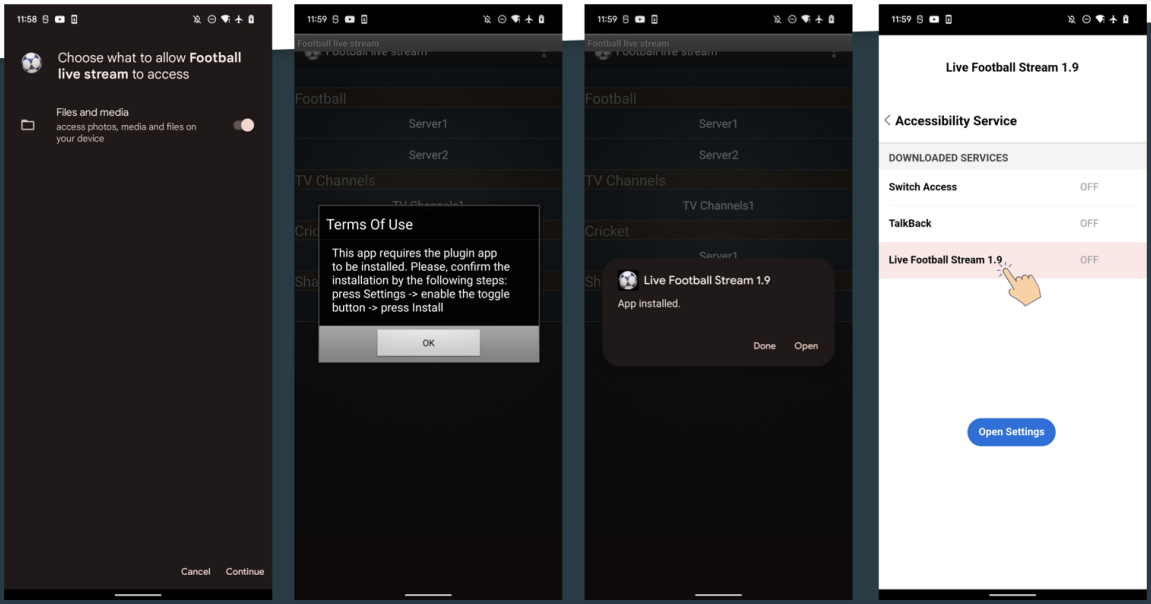
The APKs used in this campaign vary, with the analysts reporting seeing a fake live football streaming app and a modified version of the Instagram app.
These apps work as expected because the functionality of the legitimate software is not removed. Instead, Zombinder appends a malware loader to its code.
The loader is obfuscated to evade detection, so when the user launches the app, the loader will display a prompt to install a plugin. If the prompt is accepted, the loader will install a malicious payload and launch it in the background.
The Zombinder service provider claims that the malicious app bundles created with it are undetectable in runtime and can bypass Google Protect alerts or AVs running on the target devices.
The campaign drops an Ermac payload for Android, capable of performing keylogging, overlay attacks, stealing emails from Gmail, intercepting 2FA codes, and stealing crypto wallet seed phrases.
Windows malware
If the Wi-Fi authorization website visitor clicks on the “Download for Windows” button, they download Windows malware instead.
Examples seen by ThreatFabric include the Erbium stealer, the Laplas clipper, and the Aurora info-stealer.
These are all dangerous and highly capable malware strains currently under active development, rented to cybercriminals for a couple hundred USD/month.
Considering there’s overlap in the capabilities of these malware strains, the threat actors likely experiment with various tools to see what works best for them.
Commodity malware has become so easily accessible that threat actors can quickly interchange their tools and extend their portfolios just by investing more.
ThreatFabric says the wide variety of trojans delivered by the same landing pages might indicate that a single third-party malware distribution service serves multiple threat actors.









Comments
Mike_Walsh - 1 year ago
I'm SO glad I'm a "dinosaur".......and only use a dumbphone. (Which I leave at home most of the time anyway).
Astounding, isn't it? Even threat actors need to divvy up to get better stuff..! <lololol/>
NoneRain - 1 year ago
With basic knowledge in cybersecurity you avoid 99.9% of malware for end users. Then, if you put some effort with AV and an OS that receive security patches, you're actually gold.
That said, your tactic is indeed fireproof hahaha